RECENT BLOG NEWS
wolfSSL-NXP Partnership Roundup
NXP® Semiconductors N.V. is one of the wolfSSL partner network members. wolfSSL ships with support for offloading cryptographic operations onto several NXP devices (such as the Coldfire and Kinetis) that include hardware cryptography modules. Examples of these operations include utilizing the Crypto Acceleration Unit (CAU), Memory-Mapped Crypto Acceleration Unit (mmCAU), LP Trusted Crypto (LTC), and more.
Using these hardware cryptography modules leads to increased performance when compared to performing hardware cryptography within software only. These speedups increase algorithm performance greatly, and can range from 1.2 times as fast to 14.5 times as fast! In an embedded and connected world, these speedups can make all the difference for an online device or network application. Additionally, these performance increases are available when wolfSSL is being used to manage TLS 1.3 connections, giving your embedded SSL/TLS application the ability to greatly increase performance and use the most up-to-date versions of the TLS protocol.
Benchmark numbers showing the comparison of hardware crypto vs. software crypto can be viewed on the wolfSSL benchmark page, here: https://www.wolfssl.com/docs/benchmarks/. This page also includes sample benchmark data for the NXP i.MX6, and the TWR-K70F120M devices. More benchmarks, and details about wolfSSL and NXP can be viewed on the wolfSSL website: https://www.wolfssl.com/docs/nxp/
More News on wolfSSL Support for NXP
wolfSSL develops a full suite of products supporting NXP designs. Learn about wolfBoot secure boot and TLS 1.3 firmware update with FreeRTOS and wolfSSL on NXP Freedom Board K64 here. And as with every release cycle, 4.2.0 improved support for crypto hardware performance, now on NXP mmCAU (download the latest wolfSSL version 4.5.0 here!)
wolfSSL also provisions surviving FIPS certificates that can be leveraged for your i.MX8, i.MX7 and i.MX8 CAAM projects. Stay tuned for upcoming FIPS 140-3 support. Also on the roadmap, upcoming support for NXP’s SE050 hardware security chip. This is an external I2C crypto co-processor chip that supports RSA key sizes up to 4096-bit, ECC curves up to 521 bit and ED25519/Curve25519. If your target is missing, tell us!
Write to us at facts@wolfssl.com so we can learn more about your NXP projects!
wolfSSL: https://www.wolfssl.com/
NXP Semiconductors: http://www.nxp.com/
TLS 1.3: https://tools.ietf.org/html/rfc8446
Upcoming Partner Webinar with iWave
We are thrilled to announce a partner webinar with iWave!
wolfSSL and iWave have partnered together to enable embedded TLS in the iWave portfolio of embedded solutions. iWave is a global embedded solution provider that offers a wide array of rugged and high-performance System on Modules (SoMs) and Single Board Computers (SBCs) build on NXP i.MX6, i.MX8 series of Processors and INTEL FPGA series. This partnership allows iWave to strengthen their product offerings by utilizing the wolfSSL embedded SSL/TLS library and hardware crypto support, including CAAM, onto the System on Modules and embedded solutions.
Join us for this special session on:
Oct 8, 2020 07:00 AM Pacific Time (US and Canada)
Register in advance for this webinar:
https://us02web.zoom.us/webinar/register/WN_541_xJHcTueTUIgr7sWMGA
After registering, you will receive a confirmation email containing information about joining the webinar.
About Our Partner
iWave Systems Technologies Pvt. Ltd., established in the year 1999, focuses on product engineering services involving embedded hardware design and development, software development and FPGA services. iWave is a global leader in design and manufacturing of System on Modules based on NXP, Xilinx and INTEL chipsets.
Read More
https://www.iwavesystems.com/partners-with-wolfssl-enable-embedded-tls
https://www.iwavesystems.com/engineering-services/software-design-services/security.html
Blackhat Asia 2020
wolfSSL will be attending Black Hat Asia! This event will be held virtually in the Singapore Time Zone from September 29-October 2. During this week, information security experts will teach interactive, online Trainings, innovative research will be presented at Briefings, the latest open-source tools will be showcased at Arsenal, and the Business Hall will feature top-tier security solutions and service providers, plus ample networking events and opportunities.
Who We Are
wolfSSL focuses on providing lightweight and embedded security solutions with an emphasis on speed, size, portability, features, and standards compliance, such as FIPS 140-2 and 140-3, RTCA DO-178C level A certification, and support for MISRA-C capabilities. wolfSSL supports industry standards up to the current TLS 1.3 and DTLS 1.2, is up to 20 times smaller than OpenSSL, offers a simple API, an OpenSSL compatibility layer, is backed by the robust wolfCrypt cryptography library, and much more. Our products are open source, giving customers the freedom to look under the hood.
See you there!
Contact Us
Please contact us at facts@wolfssl.com with any questions about the webinar. For technical support, please contact support@wolfssl.com or view our FAQ page. As always, there will be a Q&A session following the live presentation.
Additional Resources
In the meanwhile, check out the wolfSSL embedded SSL/TLS library, star us on Github, and learn more about the latest TLS 1.3 is available in wolfSSL.
Upcoming Webinar: wolfSSL for STM32CubeMXv6
We are excited to announce our upcoming webinar: wolfSSL for STM32CubeMXv6! Join us for a 1-hour webinar to learn how wolfSSL & ST can easily integrate in STM32CubeMX projects.
You will learn:
- New features of the latest STM32CubeMX tool from ST
- How wolfSSL embedded security features set users ahead of the pack with speed, portability and feature set
- How to easily integrate wolfSSL into your project using the STM32CubeMX tool
There will be a live Q&A session at the end of the webinar where ST and wolfSSL’s experienced engineers will be available to answer your questions.
By registering for this webinar, you submit your information to STMicroelectronics and wolfSSL and their distributors, who will use it to communicate with you regarding this event and their other services.
Registration:
Session 1: Oct 1, 2020 08:00 AM Paris
Register in advance for this webinar:
https://us02web.zoom.us/webinar/register/WN_znKyIyG-SdiQ8v7pQIKncQ
OR
Session 2: Oct 1, 2020 10:00 AM Paris
Register in advance for this webinar:
https://us02web.zoom.us/webinar/register/WN_C-klzlu_R-GXaOAJXtao8Q
After registering, you will receive a confirmation email containing information about joining the webinar.
Latest updates on STMicroelectronics and wolfSSL:
wolfSSL, an ST Authorized Partner, now offers support for STM32Cube pack for STM32, adding on to previous support for the STM32 Standard Peripheral Library as well as the STM32Cube HAL (Hardware Abstraction Layer). wolfSSL also maintains and makes available an STM32Cube Expansion Package for wolfSSL to make it easy for users to pull wolfSSL directly into STM32CubeMX and STM32CubeIDE projects.
The wolfSSL embedded SSL/TLS library has support for several of the STM32 microcontrollers and for the hardware-based cryptography and random number generator offered by them as well. Our most recent update is that wolfSSL now offers support for Cube pack for STM32, adding on to previous support for the STM32 Standard Peripheral Library as well as the Cube HAL (Hardware Abstraction Layer). wolfSSL also maintains and makes available an STM32Cube Expansion Package for wolfSSL to make it easy for users to pull wolfSSL directly into STM32CubeMX and STM32CubeIDE projects.
A full list of STM32 benchmarks can be found here:
https://github.com/wolfSSL/wolfssl/tree/master/IDE/STM32Cube/STM32_Benchmarks.md
About STMicroelectronics
STMicroelectronics is a global leader in the semiconductor market serving customers across the spectrum of sense and power and automotive products and embedded processing solutions. From energy management and savings to trust and data security, from healthcare and wellness to smart consumer devices, in the home, car and office, at work and at play, ST is found everywhere microelectronics make a positive and innovative contribution to people’s life. By getting more from technology to get more from life, ST stands for life.augmented.
References
- STM32 Product Page
- STM32F2 Standard Peripheral Library Documentation
- ST STM32CubeMX
- wolfSSL STM32 Support
Read our latest blog post about how the Cube pack for STM32 is now available! – wolfSSL
Check out the wolfSSL embedded SSL/TLS library, star us on Github, and learn more about the latest TLS 1.3 is available in wolfSSL.
wolfSSL will be attending Black Hat Asia
We have exciting news, wolfSSL will be attending Black Hat Asia! This event will be held virtually in the Singapore Time Zone from September 29-October 2. During this week, information security experts will teach interactive, online Trainings, innovative research will be presented at Briefings, the latest open-source tools will be showcased at Arsenal, and the Business Hall will feature top-tier security solutions and service providers, plus ample networking events and opportunities.
As part of this event, you can attend training sessions that provide opportunities for firsthand technical skill-building taught by specialists for offensive and defensive hackers of all levels and learn the latest information security risks and trends! The virtual Business Hall offers unique opportunities for community engagement between vendors and attendees from around the world including wolfSSL! Come talk to one of our experts on TLS 1.3, embedded security, embedded SSL/TLS, Secure Boot, MQTT, SSH, TPM 2.0, curl + tiny-curl, FIPS, DO-178, MISRA and more. We’ve got the best-tested crypto on the market and the best security without sacrificing performance, so feel free to ask about our benchmarks!
We can’t wait to “see” you!
For more information about wolfSSL, our products, or future events, please contact facts@wolfssl.com.
Raccoon Attacks
If our little meme didn’t already convince you otherwise, raccoon attacks are not a big deal when it comes to wolfSSL, read more on our internal review of raccoon attacks here: https://www.wolfssl.com/wolfssl-raccoon-attack/!
To learn more about us, checkout the wolfSSL embedded SSL/TLS library, star us on GitHub, and find out more about using TLS 1.3 on wolfSSL! Contact us at facts@wolfssl.com with any questions and for technical support, email support@wolfssl.com!
wolfSSL + Tenasys INTime RTOS
Did you know that wolfSSL includes a port to the Tenasys INTime RTOS? You can read more in our original press release from Tenasys here: Secured INtime system traffic! Tenasys is using wolfSSL to secure their networked real-time systems and wolfSSL is happy to be integrated into the INTime networking stack which allows us to provide world renowned security to INTime SDK consumers.
wolfSSL also provides a FIPS 140-2 (and soon to be FIPS 140-3!) validated version of wolfCrypt! We also provide a “FIPS Ready” version of wolfSSL which is not associated with a FIPS validation, but includes FIPS-specific code. For users who may need a FIPS validated cryptography library in the future, FIPS Ready can be a good choice to make the transition as easy as possible.
If you have any questions, contact wolfSSL at facts@wolfssl.com
User-Generated Performance Advisory for Cortex M – Newlib vs Newlib-Nano
A big thank you to @eli.hughes who has shared results for their own project in hopes of further helping fellow users when building on an embedded Cortex M platform.
“I had a working project build with Segger Embedded Studio for a Nordic NRF52840 (64MHz Cortex M). We switched our build tooling to use cmake/ninja along with the newlib-nano libraries packaged with ARM GCC tools. One thing I noticed is that our TLS handshake in our application went from 3 seconds to about 16 seconds.
Using the built in wolf test functions, I was able to track down the issue.
While Segger Embedded Studio uses GCC, they have their own builds of the C standard libraries.The wolfcrypt ECC routines are very sensitive to how the C libraries are built.
Results
I could eventually get “better” performance than the SES custom library but had to use NewLib and not NewLib-nano. This results in a larger binary but the performance is much better.
wolf Test Time
Segger Embedded Studio w/ custom std libs: 208 seconds
ARM GCC Embedded w/ Newlib-Nano: 608 seconds
ARM GCC Embedded w/ Newlib: 202 seconds
ARM GCC Embedded w/ Newlib &WOLFSSL_SP_ARM_CORTEX_M_ASM : 175 seconds
In addition to using Newlib, I found the macro WOLFSSL_SP_ARM_CORTEX_M_ASM helped quite a bit. (Appears it has hand tuned ASM routines for SP math).
Apparently, newlib is built with speed optimizations and newlib-nano is built with size optimizations. I was surprised at the stark difference. I have other math heavy routines and the difference in execution speed is only 5% between -03 and -Os. It seems that the ECC SP routines have some sensitivity to the C library.
Hope this is helpful to anyone building for a Cortex M MCU.”
To read the original forum post: https://www.wolfssl.com/forums/post5456.html#p5456
Thank you @eli.hughes for sharing these findings. We hope others on the Cortex M will see this. The SP WOLFSSL_SP_ARM_CORTEX_M_ASM option is quite impressive for RSA/DH/ECC math speedups because it uses hand written assembly. At wolfSSL, we love to hear your findings and projects, so please feel free to reach out and keep us posted!
Additional Resources
Check out Eli’s article series for NXP on LPC55S69 and stay tuned for an upcoming set on cellular IoT and cloud connectivity.
Please contact us at facts@wolfssl.com for any general questions and for technical support, please contact support@wolfssl.com or view our FAQ page.
Check out the wolfSSL embedded SSL/TLS library, star us on Github, and learn more about the latest TLS 1.3 is available in wolfSSL.
QUIC WITH WOLFSSL
This post has been cross posted from Daniel Stenberg’s blog – originally posted here.
We have started the work on extending wolfSSL to provide the necessary API calls to power QUIC and HTTP/3 implementations!
Small, fast and FIPS
The TLS library known as wolfSSL is already very often a top choice when users are looking for a small and yet very fast TLS stack that supports all the latest protocol features; including TLS 1.3 support – open source with commercial support available.
As manufacturers of IoT devices and other systems with memory, CPU and footprint constraints are looking forward to following the Internet development and switching over to upcoming QUIC and HTTP/3 protocols, wolfSSL is here to help users take that step.
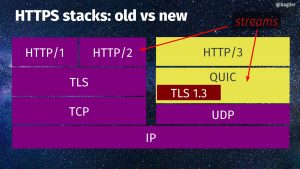
A QUIC reminder
In case you have forgot, here’s a schematic view of HTTPS stacks, old vs new. On the right side you can see HTTP/3, QUIC and the little TLS 1.3 box there within QUIC.
ngtcp2
There are no plans to write a full QUIC stack. There are already plenty of those. We’re talking about adjustments and extensions of the existing TLS library API set to make sure wolfSSL can be used as the TLS component in a QUIC stack.
One of the leading QUIC stacks and so far the only one I know of that does this, ngtcp2 is written to be TLS library agnostic and allows different TLS libraries to be plugged in as different backends. I believe it makes perfect sense to make such a plugin for wolfSSL to be a sensible step as soon as there’s code to try out.
A neat effect of that, would be that once wolfSSL works as a backend to ngtcp2, it should be possible to do full-fledged HTTP/3 transfers using curl powered by ngtcp2+wolfSSL. Contact us with other ideas for QUIC stacks you would like us to test wolfSSL with!
FIPS 140-2
We expect wolfSSL to be the first FIPS-based implementation to add support for QUIC. I hear this is valuable to a number of users.
When
This work begins now and this is just a blog post of our intentions. We and I will of course love to get your feedback on this and whatever else that is related. We’re also interested to get in touch with people and companies who want to be early testers of our implementation. You know where to find us!
I can promise you that the more interest we can sense to exist for this effort, the sooner we will see the first code to test out.
It seems likely that we’re not going to support any older TLS drafts for QUIC than draft-29.

wolfSSL offers commercial support packages and consulting for cURL and tiny-curl! Contact us at facts@wolfssl.com to learn more.
Where We’ll Be This Week
Happy Monday to our wolfSSL community! This week we will be participating in two very exciting events! Come visit us virtually to learn more about wolfSSL as well as the greater community in cryptography and embedded systems.
Events
September 21st – 24th is the virtual International Cryptographic Module Conference (ICMC20)!
ICMC is the leading event for global expertise in commercial cryptography. At ICMC20 Virtual over 400 industry leaders from 27 countries collaborate to address the challenges faced by those who develop, produce, test, specify, and use cryptographic modules. In this upcoming event, there will be a strong emphasis on standards such as FIPS 140-3, ISO/IEC 19790, eEIDAS, and Common Criteria.
To learn more:
https://icmconference.org/
September 23rd – 24th is the MtoM & Connected Objects – Embedded Systems Conference! This conference will be a virtual event surrounding embedded systems and software, display, visualization, design and testing of systems. It enables attendees to discover new technological trends, standards and regulations of IoT, MtoM and embedded systems markets and supports them in developing or deploying new projects.
Our partner AC6 will be hosting at our stand A12. Stop by to learn about this exciting new partnership and how your customers can benefit from wolfSSL training in SSL/TLS and the importance of security in embedded systems.
To learn more: https://www.salon-iot-mtom.com/
In the meanwhile, check out the wolfSSL embedded SSL/TLS library, star us on GitHub, and learn more about using TLS 1.3 in wolfSSL! Contact us at facts@wolfssl.com with any questions.
wolfSSL supports Infineon AURIX Boards
Three years ago, wolfSSL partnered with Infineon, making it easier to ensure security on Infineon-based projects. Today wolfSSL continues to foster our relationship with Infineon, including support for the latest AURIX boards.
AURIX (Automotive Real Time Integrated Next Generation Architecture) is a 32- bit Infineon microcontroller family targeting the automotive industry in terms of performance and safety. AURIX’s multicore architecture is based on up to three independent 32-bit TriCore CPUs.



Infineon designs, develops, manufactures and markets a broad range of semiconductors and system solutions. The focus of its activities is on automotive electronics, industrial electronics, mobile devices and chip card-based security. Combining entrepreneurial success with responsible action, Infineon addresses some of the most critical challenges of society: Efficient use of energy, environmentally friendly mobility and security in a connected world.
The wolfSSL embedded SSL/TLS library is a perfect fit for securing lightweight, resource-constrained devices. wolfSSL has a footprint size of 20-100kB, offers protocol support up to TLS 1.3 and DTLS 1.2, progressive algorithm support, hardware crypto support, and more.
Read more about our partnership with Infineon:
https://www.wolfssl.com/wolftpm-tested-nightly-infineon-optiga-tmp20-slb-9670/
https://www.wolfssl.com/wolfssl-announces-partnership-with-infineon/
For more information regarding wolfSSL or any additional questions, please contact facts@wolfssl.com.
In the meanwhile, check out the wolfSSLembedded SSL/TLS library, star us on GitHub, and learn more about the latestTLS 1.3 is available in wolfSSL.
Weekly updates
Archives
- April 2024 (21)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (9)
- September 2022 (7)
- August 2022 (12)
- July 2022 (11)
- June 2022 (15)
- May 2022 (11)
- April 2022 (14)
- March 2022 (12)
- February 2022 (22)
- January 2022 (13)
- December 2021 (13)
- November 2021 (29)
- October 2021 (15)
- September 2021 (15)
- August 2021 (13)
- July 2021 (21)
- June 2021 (19)
- May 2021 (12)
- April 2021 (13)
- March 2021 (27)
- February 2021 (29)
- January 2021 (22)
- December 2020 (21)
- November 2020 (14)
- October 2020 (7)
- September 2020 (22)
- August 2020 (11)
- July 2020 (8)
- June 2020 (14)
- May 2020 (15)
- April 2020 (14)
- March 2020 (4)
- February 2020 (24)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (24)
- August 2019 (21)
- July 2019 (8)
- June 2019 (13)
- May 2019 (35)
- April 2019 (31)
- March 2019 (20)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (10)
- October 2018 (18)
- September 2018 (18)
- August 2018 (8)
- July 2018 (15)
- June 2018 (29)
- May 2018 (15)
- April 2018 (11)
- March 2018 (19)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (7)
- September 2017 (8)
- August 2017 (6)
- July 2017 (11)
- June 2017 (8)
- May 2017 (10)
- April 2017 (5)
- March 2017 (7)
- February 2017 (1)
- January 2017 (8)
- December 2016 (3)
- November 2016 (2)
- October 2016 (18)
- September 2016 (8)
- August 2016 (5)
- July 2016 (4)
- June 2016 (10)
- May 2016 (4)
- April 2016 (5)
- March 2016 (4)
- February 2016 (12)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (6)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (13)
- January 2015 (6)
- December 2014 (7)
- November 2014 (3)
- October 2014 (2)
- September 2014 (11)
- August 2014 (6)
- July 2014 (9)
- June 2014 (11)
- May 2014 (11)
- April 2014 (9)
- March 2014 (3)
- February 2014 (3)
- January 2014 (5)
- December 2013 (9)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (8)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (9)
- December 2012 (13)
- November 2012 (5)
- October 2012 (7)
- September 2012 (4)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (5)
- April 2012 (7)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (6)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (8)
- May 2011 (12)
- April 2011 (4)
- March 2011 (12)
- February 2011 (8)
- January 2011 (13)
- December 2010 (17)
- November 2010 (12)
- October 2010 (14)
- September 2010 (11)
- August 2010 (20)
- July 2010 (14)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

