The AMD Versal™ Gen 1 VMK180 evaluation kit integrates Arm® Cortex®-A72 processors with programmable logic and AI engines in a single device. This article announces wolfBoot support on the VMK180, showing how a vendor-neutral secure bootloader can provide cryptographically verified boot and secure, updatable firmware for Versal-based systems.
wolfBoot Features
wolfBoot is a vendor-neutral, portable secure bootloader with advanced cryptographic capabilities:
Signature Algorithms:
- Classical: RSA (2048/3072/4096), ECC (256/384/521), Ed25519, Ed448
- Post-Quantum: LMS/HSS, XMSS and ML-DSA (Dilithium)
- Dual Signing: Hybrid classical + PQC signatures for quantum-resistant transitions
Security Features:
- Encryption: ChaCha20-Poly1305, AES-128/256 (CBC, GCM, CTR)
- Delta Updates: Binary differential updates to minimize flash writes and bandwidth
- Measured Boot: TPM integration for attestation and sealed secrets
- Anti-Rollback: Version-based protection against downgrade attacks
- Armored Mode: RAM-based bootloader with external flash verification
Platform Support: 80+ targets including ARM Cortex-M/A/R, RISC-V, x86-64, PowerPC, MIPS, Xtensa, and custom SoCs. Tested across bare-metal, RTOS (Zephyr, FreeRTOS, NuttX), and Linux environments.
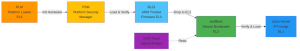
Boot Architecture
Versal employs a multi-stage boot process:
wolfBoot executes at EL2 (hypervisor mode) from DDR at address 0x8000000. By this point, PLM has completed all hardware initialization (clocks, MIO, DDR), allowing wolfBoot to focus purely on secure boot verification.
QSPI Flash Driver
The VMK180 uses dual parallel Micron MT25QU01GBBB flash chips (256MB total) with hardware striping. Key features:
- DMA mode: Hardware-accelerated transfers achieving 34 MB/s read throughput
- Quad SPI: 4-bit wide data at 75 MHz
- Cache coherency: Automatic 64-byte aligned buffer management for DMA
- Performance: Loading a 24MB signed Linux image takes ~700ms from flash
Cryptographic Boot Verification
wolfBoot implements a chain of trust using ECC384/SHA384:

Each firmware image includes a 512-byte header containing:
- Image size, version number, and timestamp
- SHA384 hash of the firmware
- ECC384 signature over the header
wolfBoot verifies signatures on every boot, selecting the partition with the higher version number. If verification fails, it falls back to the alternate partition.
Boot Performance for 24MB signed FIT image:
- Load from QSPI: ~700ms
- SHA384 integrity check: ~167ms
- ECC384 signature verification: ~3ms
- Total overhead: ~870ms
Booting Linux
wolfBoot can replace U-Boot entirely, directly loading signed Linux kernels using FIT (Flattened Image Tree) format. The complete boot flow on Versal:
The FIT image bundles the kernel and device tree. wolfBoot automatically patches the DTB’s bootargs property to specify the root filesystem: earlycon root=/dev/mmcblk0p2 rootwait
Exception Level Transition
wolfBoot runs at EL2 and can boot applications at either EL1 or EL2:
- BOOT_EL1 (default): Transitions to EL1 for Linux and most bare-metal applications
- BOOT_EL2: Boots directly at EL2 for hypervisors
Tested with PetaLinux 2024.2 – full boot to login prompt in under 10 seconds.
Firmware Updates
The dual-partition design enables safe updates:
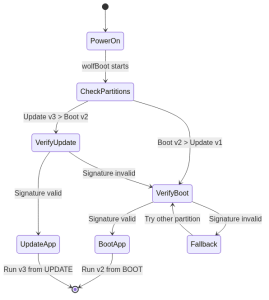
Update process:
- New firmware is written to the UPDATE partition
- On boot, wolfBoot detects the newer version
- Cryptographic verification is performed
- If valid, new firmware boots; if invalid, fallback to BOOT partition
Version anti-rollback prevents downgrade attacks. Partitions can be swapped atomically for rollback protection.
Security Considerations
wolfBoot establishes a complete chain of trust:
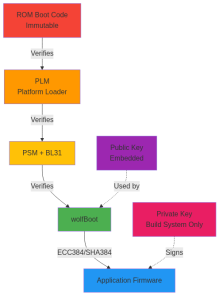
Chain of Trust:
- ROM Boot Code (immutable): Verifies PLM
- PLM: Loads and verifies PSM, BL31, wolfBoot
- wolfBoot: Verifies application signature (ECC384/SHA384)
- Application: Runs in verified state
- Application: Runs in verified state
- Signature verification: Prevents execution of tampered firmware
- Version checking: Prevents downgrade attacks
- Secure key storage: Private keys never leave build system
Conclusion
wolfBoot integration with AMD Versal provides:
- Cryptographic verification: ECC384/SHA384 signatures ensure firmware integrity
- High performance: DMA-accelerated QSPI achieves 34 MB/s throughput
- Linux boot: Direct kernel loading eliminates U-Boot dependency
- Firmware updates: Dual-partition layout with safe rollback
- Automation: Test infrastructure for CI/CD pipelines
Resources
- wolfBoot Repository
- PR #669
- Documentation: docs/Targets.md (Versal section)
- Example Config: config/examples/versal_vmk180.config
- Test Script: tools/scripts/versal_test.sh
- VMK180 Eval Kit
If you have questions about any of the above, please contact us at facts@wolfssl.com or call us at +1 425 245 8247.
Download wolfSSL Now

