Actually, no. We are not going to add another entry into our product portfolio called wolfCaliptra. There are already so many! Caliptra defines a module that includes specifications for hardware and software. To be honest, wolfSSL is a software organization, so something that would be called wolfCaliptra would fall outside the scope of what we do.
That said, we are wolves, and if we see an opportunity, we will always aggressively pursue it. In order to play in this arena, wolfSSL is implementing the software side of something that is not Caliptra, but indistinguishable from it! With the combination of wolfBoot, wolfHSM, wolfTPM, and wolfCrypt FIPS 140-3 underpinning it, the possibilities are endless. That’s right, FIPS-certified Caliptra.
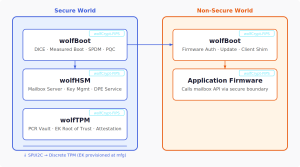
Now here is the architecture we have in mind: wolfBoot boots the application core firmware and executes wolfHSM, which can talk to wolfTPM, giving the secure world the ability to interface with the TPM. That TPM has the Endorsement Key that was generated at manufacturing time and is the Root of Trust that underpins the identity of the system.
Here is a diagram:
In the first post about Caliptra, we covered a lot of requirements and concepts that are the embodiment of Caliptra. Here is how we will cover them.
| Concept | wolfSSL Coverage |
|---|---|
| DICE | wolfBoot implements DICE layered identity derivation, producing a certificate chain where each boot stage’s identity is cryptographically bound to the measurements of what came before it. The UDS-rooted chain (IDevID → LDevID → AliasFMC → AliasRT) is built into wolfBoot’s boot sequence. |
| DPE | We are in the initial stages of implementing a custom wolfHSM request handler backed by wolfCrypt primitives, with CDI context state held in TrustZone secure-world SRAM or TPM SRAM. |
| Firmware Measurement | wolfBoot performs firmware measurement as a core function, hashing each firmware image before execution is transferred to it. When paired with wolfTPM, those measurements are extended into TPM PCR registers, creating a tamper-evident boot record. See PCR Vault below. |
| Mailbox Protocol | wolfHSM’s server loop is architecturally a mailbox protocol implementation — it waits for requests, processes them, and returns responses over an abstracted transport layer. Implementing the Caliptra mailbox command set means registering the appropriate command handlers against wolfHSM’s extensible handler API. The wolfHSM team is ready to handle this implementation. |
| OCP-LOCK | No current wolfSSL library implements OCP-LOCK, but this is fundamentally key wrapping which is the bread and butter of what we do. The attestation of erasure would be handled by wolfHSM. While requiring new work, it is not difficult to implement. |
| SPDM | wolfBoot now has interoperability with libspdm, enabling it to act as a signing oracle for SPDM responders — the exact role Caliptra plays in the datacenter attestation flow. The private keys backing SPDM signatures are held in the secure world and never exposed to application firmware. |
| PQC | wolfCrypt provides the full set of post-quantum algorithms required by Caliptra (ML-DSA-87 for signing, ML-KEM-1024 for key encapsulation) and wolfBoot already supports dual ECC + ML-DSA signatures on firmware images. |
| Root of Trust | The discrete TPM’s Endorsement Key, generated inside the TPM at manufacturing time and certified by the TPM vendor’s CA, serves as the hardware-rooted trust anchor. This is structurally identical to Caliptra’s UDS. Conceptually a secret that never leaves the chip, provisioned at the factory, with a manufacturer-signed certificate chain. |
| PCR Vault | wolfTPM implements the full TPM 2.0 PCR semantics — extend, quote, and attestation — against a discrete TPM chip that enforces the one-way accumulation property in hardware. The PCR state is held in the external TPM, which is inaccessible to application firmware, providing equivalent tamper-evidence to Caliptra’s internal PCR vault. |
Now here is where wolfSSL can really add value. All of it is FIPS 140-3 validated because everything uses wolfCrypt FIPS.
Indeed, the future of Big Iron computing is exciting! Join us in making it a reality.
If you have questions about any of the above, please contact us at facts@wolfssl.com or call us at +1 425 245 8247.
Download wolfSSL Now

