A Cipher Suite is a set of cryptographic instructions or algorithms that helps secure network connections through Transport Layer Security(TLS)/Secure Socket Layer (SSL). It helps determine how your web server will communicate secure data over HTTPS, and makes sure to secure the communications between client and server.
To start a HTTPS connect, the web server and the client perform what is a SSL handshake. The SSL handshake is a process that leverages various cryptographic functions to achieve a HTTPS connection. During the handshake, the two parties agree on a cipher suite, which is then used to secure the HTTPS connection.
During the handshake, the cipher suite typically uses these algorithms;
-
- Key Exchange Algorithm
- A method by which keys can be exchanged
- Ex: RSA, DH, ECDH, ECDHE, PSK
- Bulk Encryption Algorithm
- A method by which symmetric key algorithms will be used to encrypt data
- Ex: AES, 3DES, CAMELLIA, ARIA
- Authentication Algorithm
- A method that dictates how server authentication and client authentication is implemented
- Ex: RSA, DSA, ECDSA
- Message Authentication Code (MAC) Algorithm
- A method that determines which connections to use for data integrity checks
- Ex: SHA, MD5, POLY1305
These ciphers are used at various points of the connection to perform authentication, key generation and exchange, and a checksum to ensure integrity. The client and web server will start by deciding which specific algorithms to use in the cipher suite.
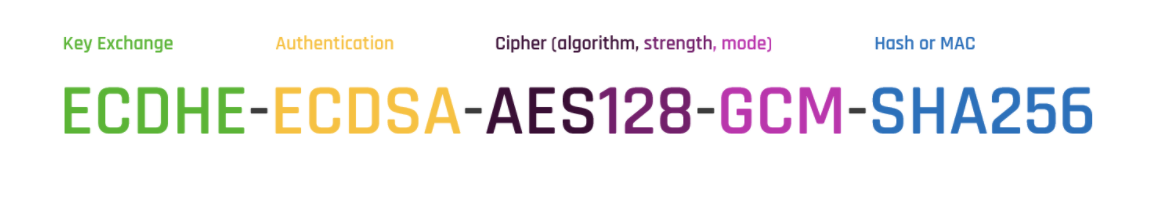
A typical Cipher Suite contains 1 key exchange, 1 bulk encryption, 1 authentication, and 1 MAC algorithm. C
Here is an example from Security Boulevard
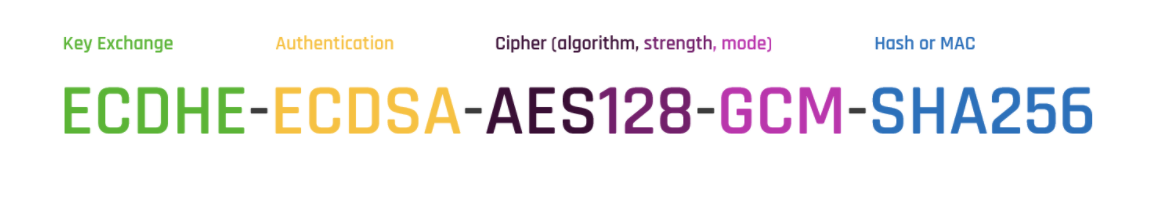 “Starting from left to right, ECDHE determines that during the handshake the keys will be exchanged via ephemeral Elliptic Curve Diffie Hellman (ECDHE). ECDSA or Elliptic Curve Digital Signature Algorithm is the authentication algorithm. AES128-GCM is the bulk encryption algorithm: AES running Galois Counter Mode with 128-bit key size. Finally, SHA-256 is the hashing algorithm.”
“Starting from left to right, ECDHE determines that during the handshake the keys will be exchanged via ephemeral Elliptic Curve Diffie Hellman (ECDHE). ECDSA or Elliptic Curve Digital Signature Algorithm is the authentication algorithm. AES128-GCM is the bulk encryption algorithm: AES running Galois Counter Mode with 128-bit key size. Finally, SHA-256 is the hashing algorithm.”
Why Cipher Suites are Important
Cipher suites are important for ensuring the security, compatibility and performance of the HTTPS connections. The cipher suite is like a recipe that dictates which algorithms to use to make secure and reliable connections.
- Security – The security level of the HTTPS traffic (or the safety of both server and client data) depends on the cipher suites the web server uses
- Compatibility – The compatibility of the HTTPS traffic (or who has access to errors, warnings etc) depends on the cipher suites the web server uses
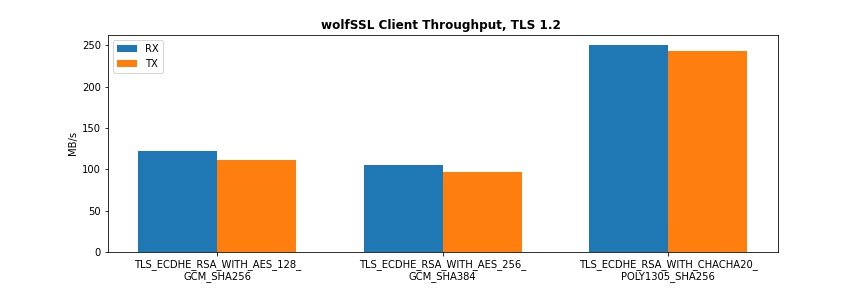
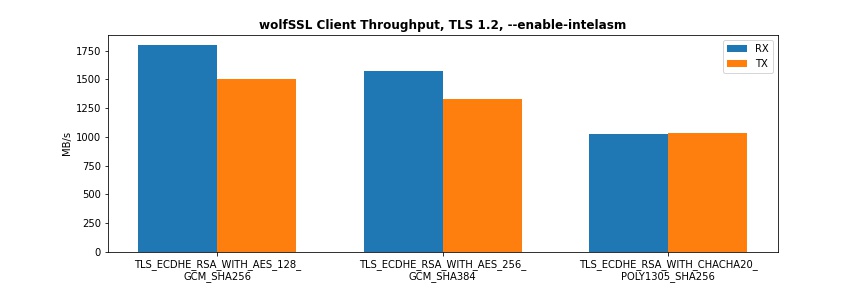
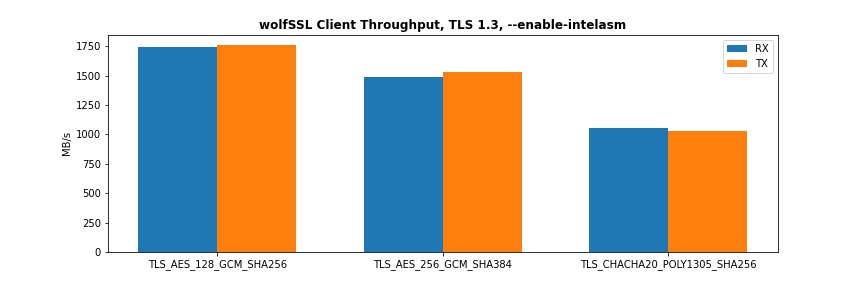
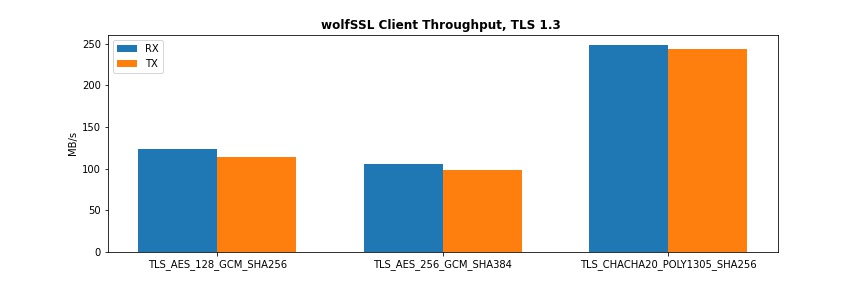
- Performance – The performance of the HTTPS traffic (or the page speed) depends on the cipher suites the web server uses.
wolfSSL and Cipher Suites
wolfSSL is modular. We’ve got two key modules: wolfSSL handles all TLS/SSL needs while wolfCrypt handles all cryptographic needs including block ciphers, stream ciphers, message digests, hashing, public key cryptography, certificates, and various helper utilities.
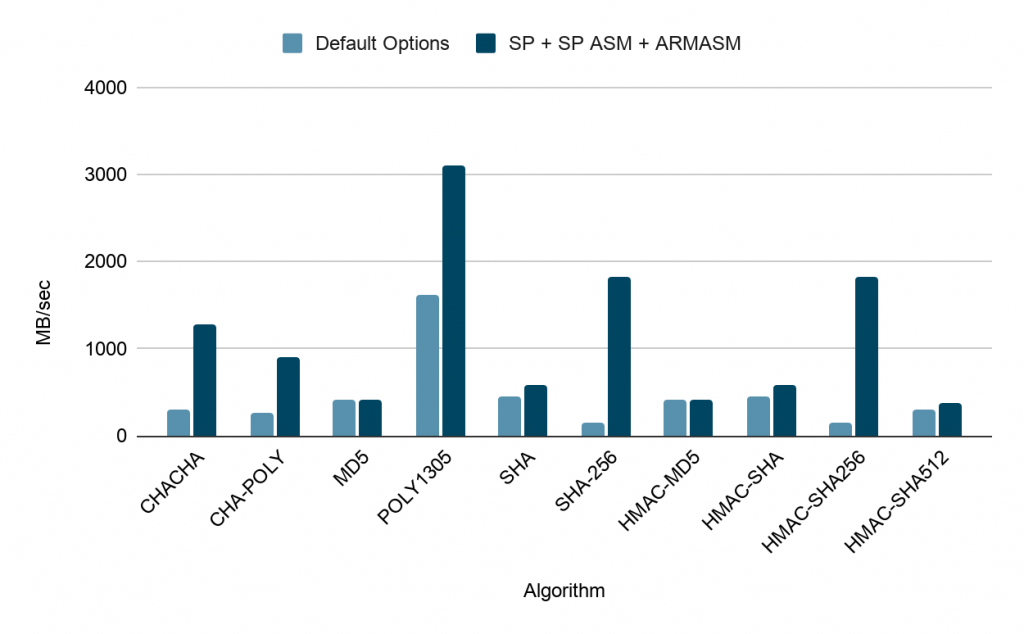
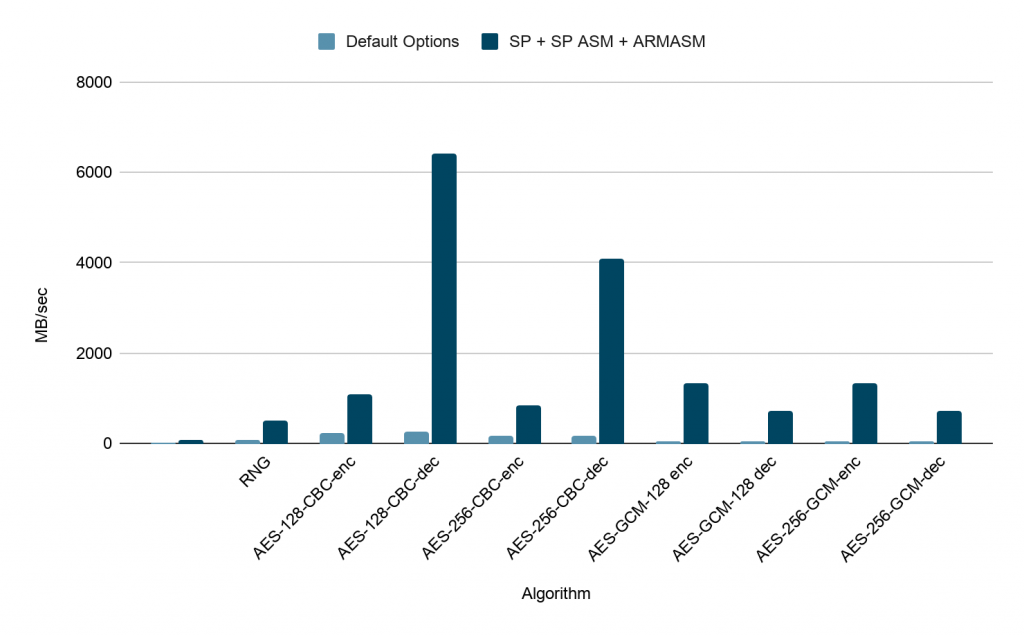
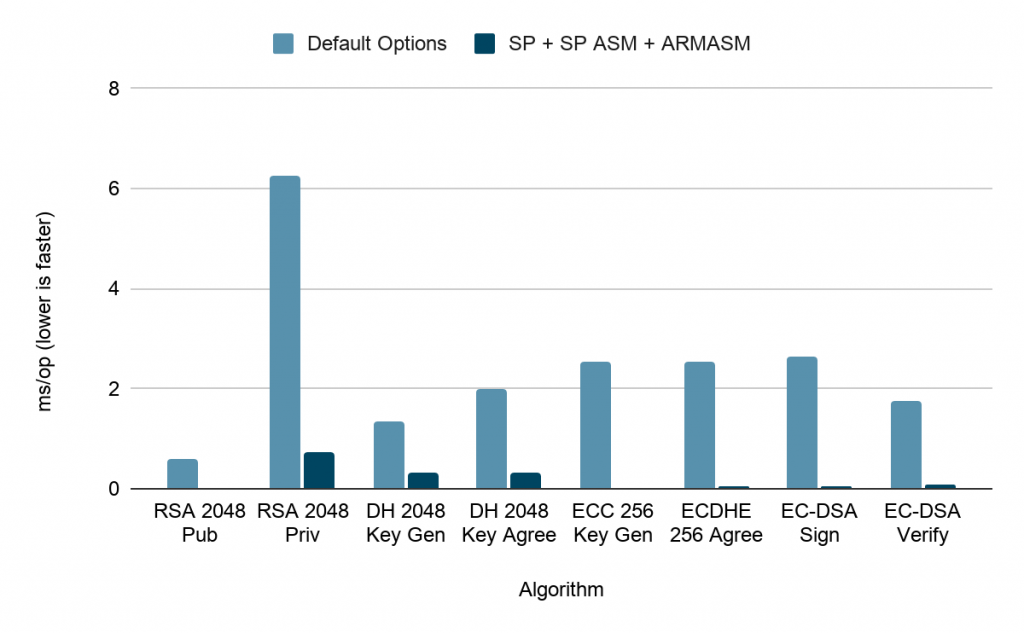
The wolfCrypt cryptography engine is a lightweight crypto library written in ANSI C and targeted for embedded, RTOS, and resource-constrained environments – primarily because of its small size, speed, and feature set. It is commonly used in standard operating environments as well because of its royalty-free pricing and excellent cross platform support. wolfCrypt supports the most popular algorithms and ciphers as well as progressive ones such as HC-128, RABBIT, and NTRU. wolfCrypt is stable, production-ready, and backed by our excellent team of security experts.
A complete description of wolfCrypt and our ciphers is available here: https://www.wolfssl.com/docs/wolfssl-manual/ch10/.
Conclusion
Cipher suites are an integral part of how websites function over HTTPS. They are a combination of ciphers used during the SSL/TLS handshake to determine the security settings of an HTTPS connection. Choosing and maintaining the appropriate cipher suites, both in the web server and the client, is important to ensure the security, performance, and compatibility of your HTTPS communications.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.


 “Starting from left to right, ECDHE determines that during the handshake the keys will be exchanged via ephemeral Elliptic Curve Diffie Hellman (ECDHE). ECDSA or Elliptic Curve Digital Signature Algorithm is the authentication algorithm. AES128-GCM is the bulk encryption algorithm: AES running Galois Counter Mode with 128-bit key size. Finally, SHA-256 is the hashing algorithm.”
“Starting from left to right, ECDHE determines that during the handshake the keys will be exchanged via ephemeral Elliptic Curve Diffie Hellman (ECDHE). ECDSA or Elliptic Curve Digital Signature Algorithm is the authentication algorithm. AES128-GCM is the bulk encryption algorithm: AES running Galois Counter Mode with 128-bit key size. Finally, SHA-256 is the hashing algorithm.”