PRODUCTS
wolfSSL JSSE Provider (and JNI wrapper)
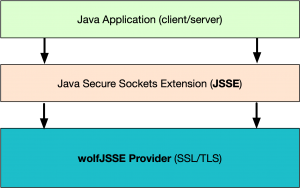
This package allows Java developers to leverage the industry-leading wolfSSL SSL/TLS implementation for secure communication, providing both a Java JSSE Provider and JNI wrapper around the native wolfSSL library. This interface gives Java applications access to all the benefits of using wolfSSL, including current SSL/TLS standards up to TLS 1.3 and DTLS 1.3, FIPS 140-3 support, performance optimizations, hardware cryptography support, and more!
wolfSSL is powered by the wolfCrypt cryptography library. A version of the wolfCrypt cryptography library has been FIPS 140-3 validated (Certificate #4718) and FIPS 140-2 validated (Certificate #3389). For additional information, visit the wolfCrypt FIPS FAQ or contact fips@wolfssl.com.
Migrating from Bouncy Castle? Check out our Bouncy Castle Migration Guide.
Get the latest open source GPLv2 version now!
Version: 1.17.0
Release Date: 04/20/2026
View ChangeLog
Highlights
- Up to TLS 1.3 and DTLS 1.3
- wolfJSSE Java JSSE Provider
- Full client and server support
- Progressive list of supported ciphers
- Key and Certificate generation
- OCSP, CRL support
- Support Available
- Long-Term Service Level Agreements available
Flexibility
- Callbacks make integration into existing applications easy
- Applications have complete control over secure communication
Time-Saving
- Eliminates need to write custom JNI
- Based on industry-leading wolfSSL
- Includes support for Android NDK and AOSP
- Tested on multiple JDKs: Oracle JDK, OpenJDK, Android, Zulu JDK, Amazon Corretto
Platform and Language Support
Native wolfSSL is built for maximum portability, is generally very easy to compile on new platforms, and has already been ported to over 30 Operating Systems! If your desired platform is not listed under the supported operating environments, please contact us, we can help out!
The native wolfSSL library is implemented the C programming language as a primary interface. This Java wrapper provides an easy and secure way for applications to use wolfSSL, which has already been tested on a number of JDK's and Operating Systems. If your JDK is not already supported, contact us for porting and verification services.
Hardware encryption and acceleration
wolfSSL also supports hardware cryptography and acceleration on several platforms. To see a list of supported platforms, please see our hardware cryptography support page. Using wolfJSSE along with hardware accelerated cryptography can provide performance improvements and footprint size reductions.
Commercial Support
Support packages for wolfSSL are available on an annual basis directly from wolfSSL. With four different package options, you can compare them side-by-side and choose the package that best fits your specific needs. Please see our Support Packages page for more details or contact us with any questions.
Benchmarks
For benchmarking information or data, please visit our wolfSSL Benchmark page or contact us for more information.
If you would like more detailed information about RAM usage, please contact us for the wolfSSL Resource Use document.
wolfSSL Training Course
Interested in getting trained by security experts on subjects related to wolfSSL and SSL/TLS? Learn more.
Features
- Java JSSE Provider
- SSL version 3.0 and TLS versions 1.0, 1.1, 1.2, and 1.3 (client and server)
- JDK Support:
- Oracle JDK, OpenJDK, Android, Zulu JDK, Amazon Corretto
- Minimal footprint size, using wolfSSL C library
- Minimal runtime memory usage
- OCSP, OCSP Stapling, and CRL support
- Supported Hash Functions:
- MD5, SHA-1, SHA-224, SHA-256, SHA-384, SHA-512, BLAKE2b, RIPEMD-160, Poly1305
- Supported Block, Stream, and Authenticated Ciphers:
- AES (CBC, CTR, GCM, CCM, GMAC, CMAC), Camellia, DES, 3DES, ARC4, ChaCha20
- Supported Public Key Algorithms:
- RSA, DSS, DH, EDH, ECDH-ECDSA, ECDHE-ECDSA, ECDH-RSA, ECDHE-RSA
- Password-based Key Derivation:
- HMAC, PBKDF2
- Curve25519 and Ed25519
- ECC and RSA Key Generation
- ECC curve types:
- SECP, SECPR2, SECPR3, BRAINPOOL, KOBLITZ
- ECC key lengths:
- 112, 128, 160, 192, 224, 239, 256, 320, 384, 512, 521
- X.509v3 RSA and ECC Signed Certificate Generation
- PEM and DER certificate support
- Hash-based PRNG
- Mutual authentication support (client/server)
- PSK (Pre-Shared Keys)
- Supported TLS Extensions:
- SNI (Server Name Indication), Maximum Fragment Length, Truncated HMAC, Supported Elliptic Curves, ALPN (Application Layer Protocol Negotiation), Extended Master Secret
- Standalone Certificate Manager
- QSH (quantum-safe handshake) extension
- Asynchronous crypto support: Intel QuickAssist, Cavium Nitrox
- Hardware Cryptography Support:
- Intel AES-NI, AVX1/2, RDRAND, RDSEED, SGX, Cavium NITROX, Intel QuickAssist, STM32F2/F4, Freescale/NXP (CAU, mmCAU, SEC, LTC), Microchip PIC32MZ, ARMv8, Renesas TSIP
- IPv4 and IPv6 support
- Abstraction Layers / User Callbacks:
- C Standard Library, Custom I/O, Memory hooks, Logging callbacks, User Atomic Record Layer Processing, Public Key
- PKCS#1 (RSA Cryptography Standard) support
- PKCS#3 (Diffie-Hellman Key Agreement Standard) support
- PKCS#5 (Password-Based Encryption Standard) support
- PKCS#7 (Cryptographic Message Syntax - CMS) support
- PKCS#8 (Private-Key Information Syntax Standard) support
- PKCS#9 (Selected Attribute Types) support
- PKCS#10 (Certificate Signing Request - CSR) support
- PKCS#11 (Cryptographic Token Interface) support
- PKCS#12 (Certificate/Personal Information Exchange Syntax Standard) support
- Long-Term Service Level Agreements available
Supported Chipmakers
- Native wolfSSL has support for chipsets including ARM, Intel, Motorola, mbed, NXP/Freescale, Microchip (PIC32)/Atmel, STMicroelectronics (STM32F2/F4), Analog Devices, Texas Instruments, and more
- If you would like to use or test wolfSSL on another chipset, let us know and we’ll be happy to support you.
Supported Operating Environments
- Linux, Mac OS X, Android (Android Studio, AOSP)
- If you would like to test wolfSSL on another environment, let us know and we’ll be happy to support you.
Licensing and Ordering:
wolfSSL is dual licensed under both the GPLv2 and commercial licensing. For more information, please see the following links.

