We are thrilled to announce a partner webinar with iWave!
wolfSSL and iWave have partnered together to enable embedded TLS in the iWave portfolio of embedded solutions. iWave is a global embedded solution provider that offers a wide array of rugged and high-performance System on Modules (SoMs) and Single Board Computers (SBCs) build on NXP i.MX6, i.MX8 series of Processors and INTEL FPGA series. This partnership allows iWave to strengthen their product offerings by utilizing the wolfSSL embedded SSL/TLS library and hardware crypto support, including CAAM, onto the System on Modules and embedded solutions.
Join us for this special session on:
Oct 8, 2020 07:00 AM Pacific Time (US and Canada)
Watch the webinar here: iWave Security IP Suite Enabled with WolfSSL
About Our Partner
iWave Systems Technologies Pvt. Ltd., established in the year 1999, focuses on product engineering services involving embedded hardware design and development, software development and FPGA services. iWave is a global leader in design and manufacturing of System on Modules based on NXP, Xilinx and INTEL chipsets.
Read More
https://www.iwavesystems.com/partners-with-wolfssl-enable-embedded-tls
https://www.iwavesystems.com/engineering-services/software-design-services/security.html
Blackhat Asia 2020
wolfSSL will be attending Black Hat Asia! This event will be held virtually in the Singapore Time Zone from September 29-October 2. During this week, information security experts will teach interactive, online Trainings, innovative research will be presented at Briefings, the latest open-source tools will be showcased at Arsenal, and the Business Hall will feature top-tier security solutions and service providers, plus ample networking events and opportunities.
Who We Are
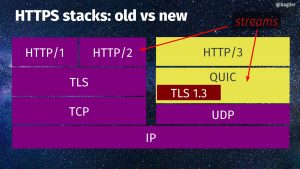
wolfSSL focuses on providing lightweight and embedded security solutions with an emphasis on speed, size, portability, features, and standards compliance, such as FIPS 140-2 and 140-3, RTCA DO-178C level A certification, and support for MISRA-C capabilities. wolfSSL supports industry standards up to the current TLS 1.3 and DTLS 1.2, is up to 20 times smaller than OpenSSL, offers a simple API, an OpenSSL compatibility layer, is backed by the robust wolfCrypt cryptography library, and much more. Our products are open source, giving customers the freedom to look under the hood.
See you there!
Contact Us
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Additional Resources
In the meanwhile, check out the wolfSSL embedded SSL/TLS library, star us on Github, and learn more about the latest TLS 1.3 is available in wolfSSL.