RECENT BLOG NEWS
Want to Comply with CNSA 2.0? Move to DTLS 1.3!
For anyone using DTLS 1.2, now might be a good time to start moving to DTLS 1.3. Why is now a good time?
- It is likely that you own both the server and the client so you have full control over the migration process.
- New post-quantum authentication (ML-DSA) and key exchange (ML-KEM) algorithms will soon be coming to both TLS and DTLS but only to version 1.3 of the protocols.
- The NSA (National Security Agency) has given the guidance in CNSA 2.0 (Commercial National Security Algorithm Suite 2.0) with timelines stating these algorithms should have already been an option and tested since the beginning of 2024 in cloud services.
- Moreover, the CNSA 2.0 guidance requires that these algorithms be the default and preferred algorithms by 2025 in cloud services.
Are you selling software that uses DTLS 1.2 to the American government agencies? If so, now is the time to move to DTLS 1.3.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
Live Webinar: What’s new in wolfBoot
Learn how wolfBoot 2.3.0 revolutionizes secure boot for embedded systems with groundbreaking features designed for quantum resistance and hybrid authentication. Join us for our upcoming webinar, What’s new in wolfBoot, on November 21st at 10 AM PT, presented by wolfSSL Software Engineer Daniele Lacamera. Gain insights into the integration of ML-DSA signature algorithms, the impact of post-quantum cryptography, and performance optimizations that elevate boot security and efficiency.
Register Today: What’s new in wolfBoot
Date: November 21st | 10 AM PT
Explore advancements that are redefining secure boot, including hybrid authentication that combines post-quantum and classic cryptographic techniques to protect against quantum threats. Discover how these innovations ensure future-proof security and compliance with the highest standards, such as CNSA 2.0.
This webinar will cover:
- Introduction of ML-DSA and its role in FIPS-204 compliance
- Implementation of hybrid authentication combining ECC/RSA and PQC
- ARM assembly optimizations for faster boot times on Cortex-M devices
- Enhanced keystore and keyvault management capabilities
- Expanded and improved hardware support, from Infineon AURIX to Nordic nRF5340
And much more…
Secure your spot now to stay ahead in embedded system security and learn from industry experts. Register Now!
As always, our webinars include Q&A throughout. If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
wolfCLU Release 0.1.6
wolfCLU release 0.1.6 is available! wolfSSL’s command line utility (wolfCLU) is a drop in replacement for the OpenSSL command line utility. It’s a handy swiss army knife of common operations used, often great for system admins or test developers. Doing things such as creating and signing certificates, generating new keys, parsing X509 certificates into human readable form, and much more. This release has seen some fixes to wolfCLU along with exciting new features. One of the new features being the addition of support for post quantum Dilithium signature generation and verification. For a full list of changes check out the ChangeLog.md.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
Join Our Live Webinar: Post-Quantum Algorithms in curl
Join us for an exclusive webinar on the cutting-edge integration of post-quantum algorithms in curl! As quantum computing advances, the need for quantum-safe cryptography is becoming critical. wolfSSL Senior Software Developer Anthony Hu will introduce essential concepts and demonstrate how to future-proof your applications against quantum threats using curl.
Register Now: Post-Quantum Algorithms in curl
Date: November 20th | 10 AM PT
Gain insights into post-quantum algorithms in curl with a hands-on demo and an in-depth exploration of key topics, including ML-KEM (FIPS 203) and ML-DSA (FIPS 204). From understanding the motivation behind CNSA 2.0 to building quantum-safe connections, this session covers the technical and practical aspects of achieving quantum resistance.
This webinar will cover:
- Why CNSA 2.0 is essential for future security
- How to build and implement post-quantum algorithms in curl
- Explanation of quantum-safe connections and supported post-quantum algorithms
And much more…
Register today for exclusive access to this in-depth webinar on post-quantum algorithms in curl! Enhance your understanding and stay ahead in the evolving landscape of quantum-safe cybersecurity.
As always, our webinars include Q&A throughout. If you have questions about any of the above, please contact us at facts@wolfssl.com or +1 425 245 8247.
Download wolfSSL Now
wolfCrypt JNI/JCE 1.7.0 Now Available
wolfCrypt JNI/JCE 1.7.0 is now available for download! This release contains a number of bug fixes, changes and new features to help better support usage from applications and 3rd party frameworks that consume wolfJCE internally.
wolfCrypt JNI/JCE allows for easy use of the native wolfCrypt cryptography library from Java. The thin JNI wrapper can be used for direct JNI calls into native wolfCrypt, or the JCE provider (wolfJCE) can be registered as a Java Security provider for seamless integration underneath the Java Cryptography API. wolfCrypt JNI/JCE can also support running on top of wolfCrypt FIPS 140-2 and 140-3 validated modules.
Changes in this release are summarized below, but please see ChangeLog.md for a full list. Watch for individual future blogs on some of these topics as well for a more in depth description.
New JCE Functionality:
- Addition of a new WolfSSLKeyStore (WKS) KeyStore implementation to help conform to FIPS 140-2 / 140-3 compliant KeyStore use
JNI and JCE Changes:
- Build compatibility has been fixed with older Java versions that do not support BigInteger.longValueExact()
- Detection of native RSA minimum key size (RSA_MIN_SIZE), and exposure of this minimum to Java via Rsa.RSA_MIN_SIZE
- Fixes to pointer use when calling the native X509CheckPrivateKey() API
Example Changes:
- Addition of a new Android Studio example IDE project, located under the “IDE/Android” directory. This can be useful as an example to see how CMakeLists.txt should be structured to build native wolfSSL and wolfCrypt JNI/JCE.
Testing Changes:
- Facebook Infer is now run on all GitHub pull requests using GitHub Actions
- Android Gradle builds are now tested on all GitHub pull requests using GitHub Actions
wolfCrypt JNI/JCE 1.7.0 can be downloaded from the wolfSSL download page, and an updated version of the wolfCrypt JNI/JCE User Manual can be found here. For any questions, or to get help using wolfSSL products in your projects, contact us at support@wolfssl.com.
If you have any questions about any of the above, please contact us at facts@wolfssl.com or call us at +1 425 245 8247.
Download wolfSSL Now
Announcing wolfHSM Integration with wolfBoot
We’re excited to announce that wolfBoot now supports integration with wolfHSM, bringing enhanced security features to our best-in-class secure bootloader solution on supported platforms. This enhancement positions wolfBoot as an even stronger tool for automotive and industrial applications with the highest security requirements.
What are wolfBoot and wolfHSM?
wolfBoot is our open-source, portable, OS-agnostic secure bootloader solution for 32-bit microcontrollers and beyond. It ensures that only authenticated firmware can run on your embedded device, providing a root of trust for your application..
wolfHSM is our generic Hardware Security Module (HSM) firmware framework, providing a unified API for secure cryptography, object storage, and key management on HSM coprocessors. wolfHSM enables applications to easily leverage a platform’s hardware-based root of trust and provides a streamlined abstraction for offloading all cryptography to the HSM coprocessor through the wolfCrypt API.
wolfHSM Integration with wolfBoot
By integrating wolfHSM with wolfBoot, we’ve enhanced the security capabilities of our already secure bootloader with the following features:
- Secure Key Storage: Cryptographic keys are now stored securely on the wolfHSM server, never accessible to wolfBoot or user applications.
- Remote Cryptographic Operations: All cryptographic operations are offloaded as remote procedure calls to the wolfHSM server. Hardware acceleration for cryptographic algorithms is included when supported by the platform.
- Flexible Key Management: Keys can be updated or rotated on the wolfHSM server without requiring a wolfBoot update.
Supported Platforms
Currently, wolfBoot supports using wolfHSM on the following platforms:
- wolfBoot simulator (using wolfHSM POSIX TCP transport)
- Infineon AURIX TC3xx (shared memory transport)
More platforms are in development. Don’t see your platform here? Reach out to us at facts@wolfSSL.com and we can discuss adding support!
Getting Started
To get started with wolfBoot + wolfHSM:
- Check out the wolfHSM integration documentation for an overview of the configuration options and HAL requirements.
- Consult your platform-specific wolfHSM documentation for instructions on configuring the wolfHSM server.
- To test wolfHSM + wolfBoot using the simulator, simply follow the instructions here to build wolfBoot with wolfHSM support and run it against our example wolfHSM server.
Give it a try and let us know what you think!
If you have any questions about wolfBoot or wolfHSM, please reach out via email at facts@wolfSSL.com or call us at +1 425 245 8247 and we will be happy to assist you!
Download wolfSSL Now
wolfSSL JNI/JSSE 1.14.0 Now Available
wolfSSL JNI/JSSE 1.14.0 is now available for download! This release contains a number of bug fixes, changes and new features to help better support usage from applications and 3rd party frameworks that consume wolfJSSE internally.
wolfSSL JNI/JSSE allows for easy use of the native wolfSSL SSL/TLS library from Java. The thin JNI wrapper can be used for direct JNI calls into native wolfSSL, or the JSSE provider (wolfJSSE) can be registered as a Java Security provider for seamless integration underneath the Java Security API. wolfSSL JNI/JSSE provides TLS 1.3 support and can also support running on top of wolfCrypt FIPS 140-2 and 140-3 validated modules.
Changes in this release are summarized below, but please see ChangeLog.md for a full list. Watch for individual future blogs on some of these topics as well for a more in depth description.
New JNI and JSSE Functionality:
- Addition of a new WKS KeyStore type to better facilitate FIPS compliance where needed
- Performance and scalability improvement with the use of native poll() set as default over select()
- Support for using RSA-PSS based certificates in TLS connections
- Addition of LDAPS endpoint identification verification to X509ExtendedTrustManager
- Two new JNI wrapped methods for native “wolfSSL_SessionIsSetup()” and “wolfSSL_SESSION_dup()”
JSSE System/Security Property Support:
- wolfjsse.debugFormat=JSON – a new System property to support outputting debug logs in JSON format, which can be more friendly for some log collection mechanisms
- wolfjsse.clientSessionCache.disabled – a new Security property to disable the Java client-side session cache, which will prevent session resumption from occurring
JSSE Changes:
- Native memory leak fixes, related to calls to wolfSSL_get_peer_certificate()
- Optimizations to allow for easier and more efficient garbage collection
- SSLEngine fixes for session storage, unwrap() FINISHED state transitions, HandshakeStatus when receiving TLS 1.3 session tickets after the handshake, correctly closing inbound on ALPN protocol name errors, and closure when fatal alerts are received
- SSLSocket fixes for end of stream handling in InputStream read() calls
- Fixes to throw expected or correct exceptions for several cases
- SSLSession getPeerCertificates() returns correct X509Certificate array
- Fixes around SSLSocket closure in a few different use cases
- Client-side session resumption is now keyed on the cipher suite and protocol in addition to host and port
- Build compatibility has been fixed with the older Android API 24, removing method calls not available in that SDK version
- A potential deadlock on close() between SSLSocket and the associated InputStream read() or OutputStream write() calls has been fixed
Exchange Changes:
- The Host String has been added into the HTTP GET request in the example ClientJSSE when used with the “-g” command line option
- JNI-only threaded client/server example applications have been added which can be helpful for seeing or debugging session resumption at the JNI-only level
- A basic RMI example client and server have been added, which can useful for reference and testing wolfJSSE over RMI
Testing Changes:
- Facebook Infer is now run on all GitHub pull requests using GitHub Actions
- TLS 1.0 and 1.1 JUnit tests are now run even if those protocols are disabled in the system “java.security” file, as long as native wolfSSL support has been compiled in
- Android Gradle builds are now tested on all GitHub pull requests using GitHub Actions
wolfSSL JNI/JSSE 1.14.0 can be downloaded from the wolfSSL download page, and an updated version of the wolfSSL JNI/JSSE User Manual can be found here. For any questions, or to get help using wolfSSL products in your projects, contact us at support@wolfssl.com.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Getting Started with wolfSSL using Visual Studio 2022

It’s never been easier to get started with wolfSSL on Microsoft Windows using Visual Studio 2022!
New VS2022-specific project and solutions files have been created for both the wolfssl/wolfcrypt core library, as well as the test and benchmark examples. These files are available immediately on GitHub and are included in the recent release.
For long term customers and backward-compatibility, we’ve had older versions of Visual Studio that generally would update to whatever latest version might be installed. See our blog post here.
Now with the new VS 2022 files, no more manual adjustments are needed. The project files work immediately out of the box. Just open the project file and click the run button.
Let’s say you’ve just cloned the latest version of wolfSSL from GitHub in your C:\workspace directory:
git clone https://github.com/wolfSSL/wolfssl
The test and benchmark examples also include a vcxproj.user file that aids in pointing the working directory of the project to the root-level wolfSSL to easily find the compiled binary.
To get started with the examples, simply navigate to the wolfCrypt benchmark directory:
C:\workspace\wolfssl\wolfcrypt\benchmark
and open either the benchmark-VS2022.vcxproj project or benchmark-VS2022.sln solution files in Visual Studio 2022.
If you happen to be one of the Windows developers that also uses WSL, you may occasionally see an oddity in Visual Studio’s equivalent of git status as compared to the result from the WSL prompt. The issue is the way Windows might handle file permissions that differ between Windows and Linux when the same file system is shared (e.g. C:\workspace vs /mnt/c/workspace), causing Visual Studio to detect modified files even though there’s no apparent text change. One way to fix this is with this git command:
git config core.fileMode false
Visual Studio may need to be re-launched if it was already already running when the command was entered in a WSL prompt.
When using wolfSSL on Windows, it is a common practice to use a user_settings.h file. There’s an example in the wolfssl/IDE/WIN directory:
https://github.com/wolfSSL/wolfssl/blob/master/IDE/WIN/user_settings.h
The wolfCrypt Benchmark and wolfCrypt Test applications can also be used as reference examples.
Note the beginning of the benchmark.c file. It uses a common pattern of including the wolfssl library:
#ifdef HAVE_CONFIG_H
#include
#endif
#ifndef WOLFSSL_USER_SETTINGS
#include
#endif
#include /* also picks up user_settings.h */
It is important to define the c-compiler preprocessor definition: WOLFSSL_USER_SETTINGS
The #include <wolfssl/wolfcrypt/settings.h> should be listed before any other wolfSSL headers are included. The user_settings.h is included in the settings.h file. The user_settings.h should never be explicitly included in any other source code header.
Beyond the Benchmark and Test Examples
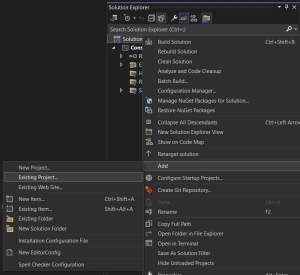
Do you have a project and you’d like to add the wolfssl library? Right-click on the solution file and select “Add – Existing Project…”:
Navigate to the root directory of your wolfSSL source code and add the wolfssl-VS2022.vcxproj file to your solution.
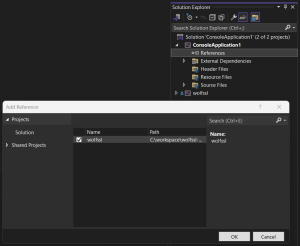
Be sure to also add a reference to each project that will use the wolfssl library. Right click on “references” and add check the “wolfssl” project:
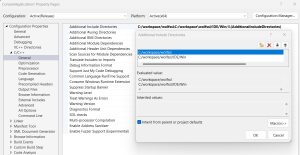
Depending on the directory structure and relative location of the project, the path to the wolfssl source code headers will likely need to be added to the Additional Include Directories. The typical example will be at least for the root directory:
C:/workspace/wolfssl
And oftentimes the user_settings.h as well, shown here in the example IDE/Win directory:
C:/workspace/wolfssl/IDE/Win
The example property page would look like this:
That’s it! Simply build and run the project.
Reorganization Coming Soon
Visual Studio project and solution files will soon be moved to the .\IDE\VS2010.\IDE\VS2022 directories.
The FIPS-related builds currently interspersed in other directories will soon be consolidated and moved to a new .\IDE-FIPS directory. See PR #8126.
For more information:
Post Quantum
Do you have code that can be upgraded to Post Quantum? See our recent blog.
FIPS Certified!
When you are ready to move on to the next step, wolfSSL will be there for you! Need to have your project NIST Certified? Recently we announced that wolfSSL is the First in the World to offer FIPS 140–3 Automated Submission with our NIST Certificate #4718.
For more details, see our blog What is FIPS (long version).
Find out more:
If you have any feedback, questions, or require support, please don’t hesitate to reach out to us via facts@wolfSSL.com, call us at +1 425 245 8247, or open an issue on GitHub.
Download wolfSSL Now
curl with FIPS 140-3 wolfSSL
cURL is a popular open-source project that is used to transfer data between client and server with URLs through various protocols. It is widely utilized and often serves as the backbone for data transfer and communication between systems. curl (the command line tool) and libcurl (the library underneath) both provide support for secure communication by leveraging SSL/TLS libraries, the FIPS 140-3 certified wolfSSL library being one of them.
With the wolfCrypt FIPS 140-3 module, wolfSSL provides and makes use of an array of cryptographic algorithms that are rigorously tested and validated under NIST’s CMVP (Cryptographic Module Validation Program). When leveraged with cURL, the result is a FIPS 140-3 compliant build with the full feature set and utility that cURL users have come to expect, in addition to the cryptographic assurance that can help them meet security standards and requirements.
Additionally, there is also the tinycurl library, designed for smaller systems and more embedded use cases. tinycurl has the same capability to utilize FIPS wolfSSL.
Are you interested in curl with FIPS 140-3 wolfSSL? Contact us!
If you have questions about any of the above or need assistance, please contact us at facts@wolfSSL.com or call us at +1 425 245 8247.
Download wolfSSL Now
Versal Support
Did you know that wolfSSL has been ported to and tested on Xilinx Versal hardware? There is support also in wolfSSL to make use of the Xilinx hardened crypto, enhancing both security and performance. Xilinx hardened crypto has accelerated crypto operations (SHA3-384 / AES-GCM / RSA / ECDSA) available on Ultrascale+ devices and is available for use with the latest and greatest Versal boards. wolfSSL makes these calls using the API from Xilinx’s XilSecure library (https://github.com/Xilinx/embeddedsw/tree/master/lib/sw_services/xilsecure) and with the addition of Versal there was minor changes to the existing calls to make use of the new features available (ECC / RNG / AES-GCM with AAD). When benchmarking we saw well over a Gigabyte per second with AES-GCM operations in our demo and improvements in performance of RSA, ECDSA, and SHA3-384 over software only implementations.
A previous white paper going into the setup and use of wolfSSL on older Ultrascale+ devices with Xilinx hardened crypto can be found here (https://docs.xilinx.com/v/u/en-US/wp512-accel-crypto). The support for Versal along with a README can be found in the wolfSSL bundle located in IDE/XilinxSDK/.
If you have questions about any of the above, please contact us at facts@wolfSSL.com or +1 425 245 8247.
Download wolfSSL Now
Weekly updates
Archives
- July 2025 (8)
- June 2025 (22)
- May 2025 (25)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

