RECENT BLOG NEWS
wolfSSL at Docker Hub
We at wolfSSL are pleased to announce that now you can use wolfSSL directly from Docker!
In a few words, Docker is a tool designed to make it easier to create, deploy, and run applications by using containers. Containers are like virtual machines, but way more lighter as the container shares some resources with the hosting machine.
We created a collection of wolfSSL containers targeting the following OSs: Debian, Ubuntu, Alpine Linux, CentOS
There are 3 different flavors of containers we have created based on each OS, they are: lib, test and examples
wolfssl/wolfssl ubuntu-examples 9198e6d82596 127MB wolfssl/wolfssl ubuntu-test ba5ca8ca4359 351MB wolfssl/wolfssl ubuntu-lib 125125eea7ab 126MB ubuntu latest 2d696327ab2e 122MB wolfssl/wolfssl debian-examples cd066ee3b5db 106MB wolfssl/wolfssl debian-test 5a3edb3a2a20 356MB wolfssl/wolfssl debian-lib 3086ef0f07b6 105MB debian latest 72ef1cf971d1 100MB wolfssl/wolfssl centos-examples 37687e96d5b9 222MB wolfssl/wolfssl centos-test 359d4195ca53 392MB wolfssl/wolfssl centos-lib a8c6cafd6205 221MB centos latest 196e0ce0c9fb 197MB wolfssl/wolfssl alpine-examples 490120f86d61 8.74MB wolfssl/wolfssl alpine-test 52b698631bec 228MB wolfssl/wolfssl alpine-lib 692a0c26cda6 7.97MB alpine latest 76da55c8019d 3.97MB
The -lib images contains only the wolfSSL binaries, while -examples also contains the test examples and -test also contains wolfSSL’s source code.
You can find further information on how to run wolfSSL examples on a docker container in our docker hub page: https://hub.docker.com/u/wolfssl/
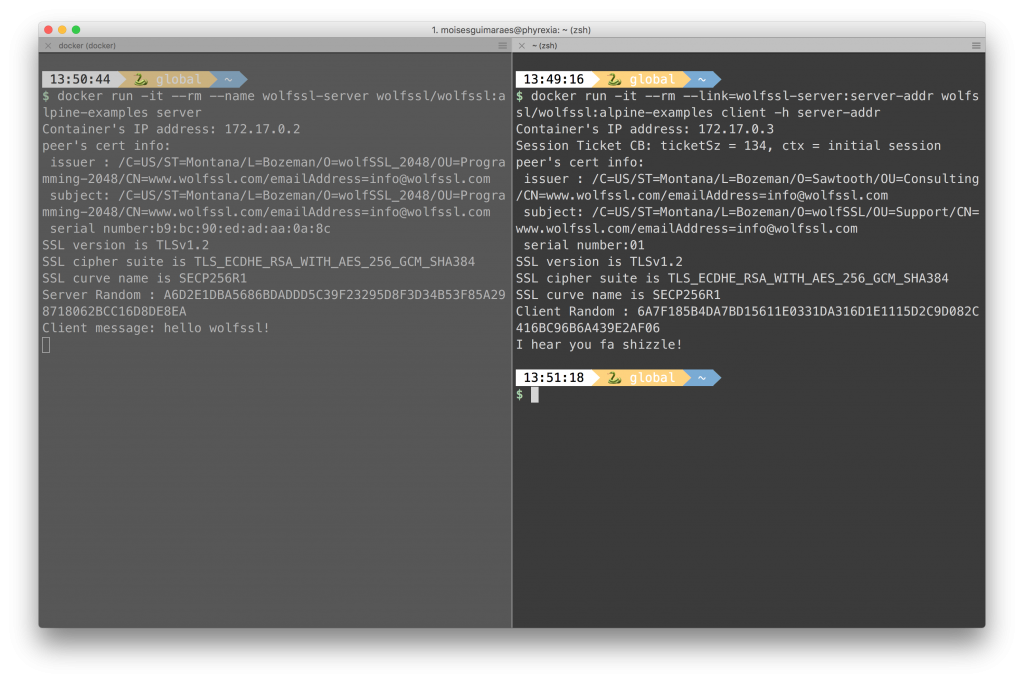
And here is a quick example, server in the left tab and the client in the right tab:
Job Posting: Embedded Systems Software Engineer
wolfSSL is a growing company looking to add a top notch embedded systems software engineer to our organization. wolfSSL develops, markets and sells the leading Open Source embedded SSL/TLS protocol implementation, wolfSSL. Our users are primarily building devices or applications that need security. Other products include wolfCrypt embedded cryptography engine, wolfMQTT client library, and wolfSSH.
Job Description:
Currently, we are seeking to add a senior level C software engineer with 5-10 years experience interested in a fun company with tremendous upside. Backgrounds that are useful to our team include networking, security, and hardware optimizations. Assembly experience is a plus. Experience with encryption software is a plus. RTOS experience is a plus. Experience with hardware-based cryptography is a plus.
Operating environments of particular interest to us include Linux, Windows, Embedded Linux and RTOS varieties (VxWorks, QNX, ThreadX, uC/OS, MQX, FreeRTOS, etc). Experience with mobile environments such as Android and iOS is also a plus, but not required.
Location is flexible. For the right candidate, we’re open to this individual working from virtually any location.
How To Apply
To apply or discuss, please send your resume and cover letter to facts@wolfssl.com.
wolfSSL Signal Protocol C Library Support

wolfSSL now supports Open Whisper Systems Signal Protocol C Library! This means that you can now develop Signal applications using wolfCrypt as the underlying cryptography provider.
For those unfamiliar with the Signal Protocol, it is described on their GitHub page as “A ratcheting forward secrecy protocol that works in synchronous and asynchronous messaging environments.”
wolfCrypt Signal Protocol Integration
By design, the Signal Protocol C Library does not depend on any SSL/TLS or cryptography library. Instead, Signal allows the application to register a crypto provider at runtime. We recently ported the wolfCrypt cryptography library into the “libsignal-protocol-c” test code and added a CMake configuration to build the libsignal-protocol-c test programs using cryptography from wolfSSL.
With this build option and wolfCrypt integration, Signal application developers can choose to use cryptography from wolfSSL instead of OpenSSL. Thanks to wolfSSL’s small footprint size, low memory usage, and broad platform support, application developers can more easily use the Signal Protocol C Library on small resource-constrained platforms and embedded systems.
For more information on using wolfCrypt with Signal, contact us at facts@wolfssl.com!
Securing MySQL (#mysql) with wolfSSL SSL/TLS


MySQL (#mysql) currently comes bundled with yaSSL to provide an option for SSL/TLS connections when using a database. A patch for securing MySQL with the wolfSSL embedded SSL/TLS library is available for MySQL version 8.0.0 here https://github.com/wolfSSL/mysql-patch.
Along with an increased level of security comes the potential to use progressive features offered by wolfSSL – such as TLS 1.3 and ChaCha20 / Poly1305 AEAD cipher suites (ex: ECDHE-RSA-CHACHA20-POLY1305). Another great feature is that wolfSSL cryptography is FIPS 140-2 validated! The change from yaSSL to wolfSSL will fit nicely into both Open Source and commercial applications, as it is dual licensed under both GPLv2 and standard commercial license terms.
For more information about the port, or to provide us feedback, contact us at facts@wolfssl.com!
wolfSSL is Expanding Our OpenSSL Compatibility Layer
Tired of using OpenSSL? Recently wolfSSL has been expanding our compatibility layer, which means that it soon will be even easier to replace OpenSSL with wolfSSL in existing projects. In some cases the replacement can be as easy as including <wolfssl/options.h> and linking to a wolfSSL library that has been compiled with –enable-opensslextra.
For more information about the wolfSSL or the compatibility layer contact us at facts@wolfssl.com.
Transport-Level Security Tradeoffs using MQTT
By Todd Ouska, wolfSSL
The Message Queuing Telemetry Transport protocol, or MQTT, has become a favorite of Internet of Things (IoT) developers, and why not? It’s incredibly lightweight (on the order of a couple Kb for client implementations), has easy-to-use APIs, and is available for free under the Eclipse Public License (EPL). If your connected application is something simple and relatively contained – like remote monitoring the temperature in your living room, for example – that much is probably enough to make you happy.
But what if your application is a little more complex? Say you’re combining multiple sensors, an HVAC system, a little intelligence, and MQTT to automatically adjust the climate in your home based on occupancy, and you’ve also configured remote management into the application so you can manually override instances where your dog tripped the infrared proximity sensor (sorry, Spot). Or maybe after some hard work you’re deploying a similar commercial system and need to update a sensor platform’s firmware to provide more precise measurements. So at what point is “enough” good enough? The answer depends on you and your application.
MQTT is a publish/subscribe protocol, meaning that would-be “clients” in the traditional networking model can act as both publishers of and subscribers to messages related to particular topics. Messages are distributed using the transmission control protocol (TCP), but rather than being indiscriminately broadcast, clients send messages through a central MQTT broker that accepts messages from a publisher and distributes them to the subscriber(s) to that topic at varying quality of service (QoS) levels.
However, in order to keep the protocol as lightweight as possible for resource-constrained IoT edge devices, the MQTT specification offers nothing on top of TCP for security outside of a recommendation that the transport layer security (TLS) protocol be used for applications that require additional levels of authentication. As a result, MQTT communications that rely on TCP alone are unencrypted and susceptible to man-in-the-middle attacks.
To illustrate what this means in more detail, let’s go back to our two “complex” examples from earlier. Say a proximity sensing platform publishes a message to the MQTT broker with the topic “home/occupancy.” The MQTT protocol does allow the use of a username and password for client identification, but these are displayed in text if some form of encryption isn’t used. Therefore, an eavesdropper could potentially impersonate a client subscriber and decrypt a message payload, or even imitate a client publisher and issue fake or modified messages. In terms of the personal home application this could signal to prospective thieves that no one is home, and in the commercial deployment scenario has serious implications on processes like remote firmware updates.
TLS tradeoffs
As mentioned, the MQTT protocol does recommend the use of TLS for more sensitive MQTT implementations, and a network port (port 8883) has even been reserved for this purpose. TLS is the successor of the secure sockets layer (SSL) protocol, and provides an encrypted communication channel over which MQTT messages can be sent. Before the channel is established TLS uses a handshake to pass certificates (or keys) from the publisher to the broker, but also between the broker and subscribers. If successful a secure channel is established, if not, the connection is aborted. Easy enough, right?
Well, maybe not. The downside of using TLS, SSL, and other methods of encryption is that they can add significant overhead, which is probably why you chose to use MQTT in the first place. For example, at wolfSSL we recently released an MQTT client library (wolfMQTT) with a compiled size of 3.6 kB. A TLS handshake alone can consume that much, without accounting for the encryption overhead on the individual packets themselves. For certain resource-constrained embedded devices, particularly those based on small microcontrollers, this added workload can simply consume too much in terms of CPU resources.
Techniques such as session resumption can compensate for some of the connection costs of TLS, and hardware acceleration is also a method for reducing the size penalty for encryption. Another important consideration is selecting an optimized encryption library when securing system communications, and in the case of wolfMQTT, integrating the lightweight wolfSSL embedded SSL/TLS library resulted in a compiled size of 20-30 kB when paired with hardware acceleration.
In the end, the decision when and how to implement security in your MQTT-based IoT system depends on you and your application. If you decide to move forward with transport-layer encryption, some best practices include working with MQTT libraries that are open source and allow you to look under the hood, but also provide documentation and examples of how encryption could be implemented in your application. If you’re a commercial entity using MQTT, make sure to partner with a vendor that has security credentials and also supports the widest range of operating systems and embedded chipsets possible in order to avoid lock-in.
For more, check out our secure firmware update example written in C that demonstrates encrypted communications to and from an MQTT broker using TLS.
For more information about wolfSSL and wolfMQTT, or about some of our other products (wolfSSH, wolfCrypt), contact us at facts@wolfssl.com
Todd Ouska is Co-Founder and CTO of wolfSSL.
wolfSSL
LinkedIn: https://www.linkedin.com/company/wolfssl/
Facebook: www.facebook.com/wolfssl
Top Reasons to use the wolfSSL patch in MySQL instead of yaSSL or OpenSSL
- You want TLS 1.3 support for connections.
- You want to avoid the steady stream of security updates required by using OpenSSL.
- You are concerned about the effect of quantum computers on security and want to use quantum safe crypto.
- You are performance driven, and want to leverage the latest performance enhancements and hardware crypto support.
- You want direct support for the crypto you use in MySQL or MariaDB.
- You need FIPS 140-2 support for your MySQL install.
You can check out the patch here. If you have questions or need support, then give us a call at +1 425 245 8247 or email us at facts@wolfssl.com.
wolfSSL 3.13.0 Now Available
wolfSSL 3.13.0 is now available for download! wolfSSL 3.13.0 includes bug fixes and new features, including support for TLS 1.3 Draft 21, performance and footprint optimizations, build fixes, updated examples and project files, and one vulnerability fix.
Continue reading below for a summary of the features and fixes included in this release!
Protocol Changes:
* Fixes for TLS 1.3, support for Draft 21
* TLS 1.0 disabled by default, addition of “–enable-tls10” configure option
Performance and Size Optimizations:
* New option to reduce SHA-256 code size at expense of performance (USE_SLOW_SHA256)
* New option for memory reduced build (–enable-lowresource)
* AES-GCM performance improvements on AVX1 (IvyBridge) and AVX2
* SHA-256 and SHA-512 performance improvements using AVX1/2 ASM
* SHA-3 size and performance optimizations
* Fixes for Intel AVX2 builds on Mac/OSX
* Intel assembly for Curve25519, and Ed25519 performance optimizations
* Allow adjusting static I/O buffer size with WOLFMEM_IO_SZ
Build Option Updates:
* New option to force 32-bit mode with “–enable-32bit”
* New option to disable all inline assembly with “–disable-asm”
* Ability to override maximum signature algorithms using WOLFSSL_MAX_SIGALGO
* Removes 3DES and SHA1 dependencies from PKCS#7
* Adds ability to disable PKCS#7 EncryptedData type (NO_PKCS7_ENCRYPTED_DATA)
Feature Additions:
* Add ability to get client-side SNI
* Expanded OpenSSL compatibility layer
* Adds static memory support to the wolfSSL example client
* Adds option to wolfCrypt benchmark to benchmark individual algorithms
* Adds option to wolfCrypt benchmark to display benchmarks in powers of 10 (-base10)
Updated Project Files:
* Updated Visual Studio for ARM builds (for ECC supported curves and SHA-384)
* Updated Texas Instruments TI-RTOS build
* Updated STM32 CubeMX build with fixes for SHA
* Updated IAR EWARM project files
* Updated Apple Xcode projects with the addition of a benchmark example project
Build and Feature Fixes:
* Fixes for handling of unsupported TLS extensions.
* Fixes for compiling AES-GCM code with GCC 4.8.*
* Fixes for building without a filesystem
* Fix for logging file names with OpenSSL compatibility layer enabled, with
WOLFSSL_MAX_ERROR_SZ user-overridable
* Fixes for sniffer to use TLS 1.2 client method
Vulnerability Fix:
This release of wolfSSL fixes 1 security vulnerability.
wolfSSL is cited in the recent ROBOT Attack by Böck, Somorovsky, and Young. The paper notes that wolfSSL only gives a weak oracle without a practical attack but this is still a flaw. This release contains a fix for this report. Please note that wolfSSL has static RSA cipher suites disabled by default as of version 3.6.6 because of the lack of perfect forward secrecy. Only users who have explicitly enabled static RSA cipher suites with WOLFSSL_STATIC_RSA and use those suites on a host are affected. More information will be available on our website at:
https://wolfssl.com/wolfSSL/security/vulnerabilities.php
For additional documentation, please visit our Docs page, or contact us at facts@wolfssl.com.
wolfSSL Xilinx Support
wolfSSL now supports Xilinx SoCs and FPGAs. The wolfSSL embedded SSL/TLS library can be used with FPGAs which use the MicroBlaze CPU and/or Zynq and Zynq UltraScale+ SoCs. Improved performance speeds with using the hardware crpyto can be seen. Increasing AES-GCM, RSA, and SHA3 operations performance. In addition to the performance gained a user also gets the additional security the hardware provides while executing the algorithms.
For more information contact facts@wolfssl.com
Job Posting: Embedded Systems Software Engineer
wolfSSL is a growing company looking to add a top notch embedded systems software engineer to our organization. wolfSSL develops, markets and sells the leading Open Source embedded SSL/TLS protocol implementation, wolfSSL. Our users are primarily building devices or applications that need security. Other products include wolfCrypt embedded cryptography engine, wolfMQTT client library, and wolfSSH.
Job Description:
Currently, we are seeking to add a senior level C software engineer with 5-10 years experience interested in a fun company with tremendous upside. Backgrounds that are useful to our team include networking, security, and hardware optimizations. Assembly experience is a plus. Experience with encryption software is a plus. RTOS experience is a plus. Experience with hardware-based cryptography is a plus.
Operating environments of particular interest to us include Linux, Windows, Embedded Linux and RTOS varieties (VxWorks, QNX, ThreadX, uC/OS, MQX, FreeRTOS, etc). Experience with mobile environments such as Android and iOS is also a plus, but not required.
Location is flexible. For the right candidate, we’re open to this individual working from virtually any location.
How To Apply
To apply or discuss, please send your resume and cover letter to facts@wolfssl.com.
Weekly updates
Archives
- July 2025 (15)
- June 2025 (22)
- May 2025 (25)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

