RECENT BLOG NEWS
lighttpd Upstream Support
lighttpd has added support for wolfSSL in version 1.4.51! lighttpd is a fast and lightweight web server designed with a very low memory footprint. These design goals make wolfSSL an excellent choice as the SSL/TLS implementation, as it’s built to be lightweight, portable, and very fast. wolfSSL targets embedded and IoT devices but works just as well on desktop, enterprise, and cloud environments. Configuring wolfSSL as the SSL/TLS backend for lighttpd is simple and can provide you with the immediate benefit of a lower memory footprint and faster cryptography!
Compile wolfSSL with:
./configure --enable-lighty make make install
Compile lighttpd with:
./configure --with-wolfssl make make install
To learn about how to setup your lighttpd instance to use wolfSSL, please visit https://redmine.lighttpd.net/projects/lighttpd/wiki/Docs_SSL.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Love it? Star us on GitHub!
Open Source Project Ports: NTP
Because of the exceptional portability of our wolfCrypt library, plus our fantastic team of engineers, we’re able to frequently add new ports. We’ll be showcasing a few of the latest open source project ports over the next ten weeks, so tune in!
First, we just integrated wolfSSL with the NTP (Network Time Protocol) project. This port allows for the use of NTP with our FIPS-validated crypto library, wolfCrypt. NTP is designed to synchronize the clocks of computers over packet-switched, variable-latency data networks. For more information on NTP, you can also visit the project’s website at ntp.org.
We’ve enabled NTP to be able to call into wolfSSL through the OpenSSL compatibility layer. You can access the GitHub page here: https://github.com/wolfSSL/osp/tree/master/ntp/4.2.8p15
Need more? Subscribe to our YouTube channel for access to wolfSSL webinars!
Love it? Star us on GitHub!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
ECIES – SEC.1 and ISO/IEC 18033
The wolfSSL library has for a long time supported encryption and decryption using ECC with an implementation of ECIES (Elliptic Curve Integrated Encryption Scheme). Recently the ECIES code was updated to support the SEC.1 and ISO/IEC 18033 variants.
ECIES is the elliptic curve equivalent of the RSA encryption algorithm and is useful as a key encapsulation mechanism (KEM). KEMs are used to established shared keys between two parties that have never communicated before. By securing, say, a symmetric key with the EC public key, only the owner of the EC private key can derive it.
Unlike RSA encryption, ECIES can also be used for sending a message securely to the owner of the private key (i.e. data encapsulation mechanism (DEM)). The integration of a symmetric cipher in the ECIES algorithm allows it to encrypt any amount of data.
In the real world, ECIES is used by standards like the Intelligent Transport Systems (ETSI TS 103 097) and is part of Android Pay and Apple’s iMessage and Find My.
In the wolfSSL library, the default algorithm is now as described in SEC.1. If you require the original wolfSSL algorithm then configure with -–enable-ecies=old or define WOLFSSL_ECIES_OLD. Alternatively, if the ISO/IEC 18033 algorithm is required then configure with -–enable-ecies=iso18033 or define WOLFSSL_ECIES_ISO18033.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Sniffing traffic with TLS v1.3
The wolfSSL library includes a useful tool for sniffing TLS traffic. This can be used to capture and decrypt live or recorded PCAP traces when at least one of the keys is known. Typically a static RSA ciphersuite would be used, however with TLS v1.3 only Perfect Forward Secrecy (PFS) ciphers are allowed. For TLS v1.3 all cipher suites use a new ephemeral key for each new session.
In order to solve this we added a “static ephemeral” feature, which allows setting a known key that is used for deriving a shared secret. The key can be rolled periodically and synchronized with the sniffer tool to decrypt traffic. This feature is disabled by default and is only recommended for internal or test environments.
As a proof of concept we added this support to Apache httpd to demonstrate real-time decryption of web traffic. We are also working on a key manager to assist with key rolling and synchronization.
A use case that might be interesting is a company internal web server that requires auditing.
The TLS v1.3 sniffer support was added in PR 3044 and officially supported in v4.8.1.
The Apache httpd branch with sniffer and FIPS ready support is here.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfSSL supports IoT SAFE
The wolfSSL embedded SSL/TLS library supports many popular hardware secure elements from several suppliers using different technologies.
Some of these hardware elements are specifically designed to enable end-to-end security in IoT devices, by providing a hardware ‘Root of Trust’, and by providing asynchronous cryptography functionality and key vaults.
GSMA is an alliance representing mobile operators, manufacturers and companies focusing on the mobile communication industry. The alliance has published the guidelines to implement a Root-of-trust mechanism, IoT SIM Applet For Secure End-to-End Communication, also known as IoT-SAFE. This technology promotes the use of SIM cards as Root-of-Trust to secure applications and services running on embedded systems connected through the mobile network. IoT-SAFE opens new possibilities for key provisioning through a component that is, in fact, already designed to support end-to-end security within different layers of the protocol.
wolfSSL, in collaboration with partners in the mobile industry, has recently developed an IoT-SAFE module for the wolfSSL embedded TLS library.
The code is portable and it’s designed to be used on an embedded board, equipped with an LTE modem and an IoT-SAFE capable SIM card, but can be easily adapted to run on any environment that has access to a communication channel with an IoT-SAFE capable SIM card.
The module includes several features, such as the possibility to use IoT-SAFE as true random number generator, access asymmetric key operations on the SIM, as well as generate, store and retrieve keys in the secure vault. The most important feature though, is the possibility to equip wolfSSL sessions with IoT-SAFE support, so that all the operations during the TLS handshake for that session are executed through IoT-SAFE commands.
To demonstrate a full TLS endpoint using IoT-SAFE API to complete the handshake and establish a TLS session, we have prepared an example that uses a SIM card pre-provisioned with our test ECC certificate and keys. Both TLS 1.3 and 1.2 are supported.
Securing Device-to-Cloud communication with a robust end-to-end strategy is of course the main priority of this module. However, we are looking forward to seeing wolfSSL IoT-SAFE support used in different applications and use cases.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Need more? Subscribe to our YouTube channel for access to wolfSSL webinars!
Love it? Star us on GitHub!
wolfSSL in ExpressVPN’s Lightway
ExpressVPN’s Lightway protocol is out of beta and leverages wolfSSL for secure crypto. As such, the “modern VPN” inherits speed, performance, best-tested security and is able to maintain it’s lightweight mobility.
“In terms of the encryption, [ExpressVPN’s Chief Architect, Pete] Membrey explained that Lightway uses wolfSSL. ‘To be clear, we didn’t roll any of our own crypto. It’s something we – as a principle – keep well away from. It’s extremely easy to get that wrong so we outsourced it, effectively, to a library that’s open source and has been audited.’
wolfSSL is used on millions of devices already and is the library that powers Pokémon GO. It’s designed for embedded devices, so it’s fast on Apple M1 chip, on routers, iPhones and more.”
Learn more about ExpressVPN’s announcement on their blog and TechAdvisor.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Need more? Subscribe to our YouTube page for access to webinars.
Love it? Star us on GitHub!
What is a Block Cipher?
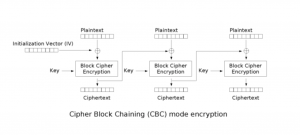
A block cipher is an encryption method that applies a deterministic algorithm along with a symmetric key to encrypt a block of text, rather than encrypting one bit at a time as in stream ciphers. For example, a common block cipher, AES (Advanced Encryption Standard), encrypts 128 bit blocks with a key of predetermined length: 128, 192, or 256 bits. Block ciphers are pseudorandom permutation (PRP) families that operate on the fixed size block of bits. PRPs are functions that cannot be differentiated from completely random permutations and thus, are considered reliable, until proven unreliable.
Block cipher modes of operation have been developed to eliminate the chance of encrypting identical blocks of text the same way, the ciphertext formed from the previous encrypted block is applied to the next block. A block of bits called an initialization vector (IV) is also used by modes of operation to ensure ciphertexts remain distinct even when the same plaintext message is encrypted a number of times.
Some of the various modes of operation for block ciphers include CBC (cipher block chaining), CFB (cipher feedback), CTR (counter), and GCM (Galois/Counter Mode), among others. AES, described above, is an example of a CBC mode where an IV is crossed with the initial plaintext block and the encryption algorithm is completed with a given key, and the ciphertext is then outputted. This resultant cipher text is then used in place of the IV in subsequent plaintext blocks.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
References
[1] Pseudorandom permutation. (2014, November 23). In Wikipedia, The Free Encyclopedia.Retrieved 22:06, December 18, 2014, from http://en.wikipedia.org/w/index.php?title=Pseudorandom_permutation&oldid=635108728.
[2] Margaret Rouse. (2014). Block Cipher [Online]. Available URL: http://searchsecurity.techtarget.com/definition/block-cipher.
[3] Block cipher mode of operation. (2014, December 12). In Wikipedia, The Free Encyclopedia. Retrieved 22:17, December 18, 2014, from http://en.wikipedia.org/w/index.php?title=Block_cipher_mode_of_operation&oldid=637837298
[4] Wikimedia. (2014). Available URL: http://upload.wikimedia.org/wikipedia/commons/d/d3/Cbc_encryption.png.
What is a Stream Cipher?
A stream cipher encrypts plaintext messages by applying an encryption algorithm with a pseudorandom cipher digit stream (keystream). Each bit of the message is encrypted one by one with the corresponding keystream digit. Stream ciphers are typically used in cases where speed and simplicity are both requirements. If a 128 bit block cipher (such as AES [Advanced Encryption Standard]) were to be used in place of a stream cipher where it was encrypting messages of 32 bit blocks, 96 bits of padding would remain. This is an inefficient approach and is one reason why a stream cipher would be preferred over a block cipher, since stream ciphers operate on the smallest possible unit.
Some common stream ciphers include Salsa20, ChaCha (a seemingly better variant of Salsa20), Rabbit, and HC-256, among others. Block ciphers can be used in stream mode to act as a stream cipher. If a block cipher is run in CFB (cipher feedback), OFB (output feedback), or CTR (counter) mode, it does not require additional measures to handle messages that aren’t equivalent to the length of multiples of the block size, and eliminates the padding effect.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
References
[1] Stream cipher. (2014, November 19). In Wikipedia, The Free Encyclopedia. Retrieved 16:19, December 19, 2014, from http://en.wikipedia.org/w/index.php?title=Stream_cipher&oldid=634494612.
[2] Margaret Rouse. Stream Cipher. (2005). Available URL: http://searchsecurity.techtarget.com/definition/stream-cipher.
[3] Block cipher mode of operation. (2014, December 12). In Wikipedia, The Free Encyclopedia. Retrieved 17:13, December 19, 2014, from http://en.wikipedia.org/w/index.php?title=Block_cipher_mode_of_operation&oldid=637837298.
strongSwan + wolfSSL + FIPS!
As some may be aware, wolfSSL added support for strongSwan in April of 2019. The upstream commit can be reviewed here: https://github.com/strongswan/strongswan/pull/133
Users can test the latest development master of wolfSSL with the latest version of strongSwan using the following setup:
wolfSSL Build and Installation Steps
$ git clone https://github.com/wolfSSL/wolfssl.git $ cd wolfssl $ ./autogen.sh $ ./configure --enable-opensslall --enable-keygen --enable-rsapss --enable-des3 --enable-dtls --enable-certgen --enable-certreq --enable-certext --enable-sessioncerts --enable-crl --enable-ocsp CFLAGS="-DWOLFSSL_DES_ECB -DWOLFSSL_LOG_PRINTF -DWOLFSSL_PUBLIC_MP -DHAVE_EX_DATA" $ make $ make check $ sudo make install
strongSwan Build and Installation Steps
# if the following packages are not already installed: $ sudo apt-get install flex bison byacc libsoup2.4-dev gperf $ git clone https://github.com/strongswan/strongswan.git $ cd strongswan $ ./autogen.sh # if packages are missing autogen.sh must be re-run $ ./configure --disable-defaults --enable-pki --enable-wolfssl --enable-pem $ make $ make check $ sudo make install
wolfSSL has had interest in enabling FIPS 140-2/140-3 support with strongSwan so our engineers verified everything is working with the wolfCrypt FIPS 140-2 validated Module!
The steps wolfSSL used for testing are as follows:
Testing was done using the wolfSSL commercial FIPS release v4.7.0 which internally uses the wolfCrypt v4.0.0 FIPS 140-2 validated Crypto Module. It was located in the /home/user-name/Downloads directory on the target test system, Linux 4.15 Ubuntu 18.04 LTS running on Intel(R) Xeon(R) CPU E3-1270 v6 @ 3.80GHz.
- wolfSSL was configured and installed with these settings:
./configure --enable-opensslall --enable-keygen --enable-rsapss --enable-des3 --enable-dtls --enable-certgen --enable-certreq --enable-certext --enable-sessioncerts --enable-crl --enable-ocsp CFLAGS="-DWOLFSSL_DES_ECB -DWOLFSSL_LOG_PRINTF -DWOLFSSL_PUBLIC_MP -DHAVE_EX_DATA -DFP_MAX_BITS=8192" --enable-ed25519 --enable-curve25519 --enable-fips=v2 --enable-intelasm --prefix=$(pwd)/../fips-install-dir make make install
- A custom install location was used which equated to
/home/user-name/Downloads/fips-install-dirand the configuration for strongSwan accounted for this. - strongSwan was cloned to
/home/user-name/Downloadswith “git clone https://github.com/strongswan/strongswan.git” - StongSwan was configured and installed with these settings:
./configure --disable-defaults --enable-pki --enable-wolfssl --enable-pem --prefix=$(pwd)/../strongswan-install-dir wolfssl_CFLAGS="-I$(pwd)/../fips-install-dir/include" wolfssl_LIBS="-L$(pwd)/../fips-install-dir/lib -lwolfssl" make make install make check
- In the make check stage of the test, it was observed that 1 test was failing.
Passed 34 of 35 'libstrongswan' suites FAIL: libstrongswan_tests ================== 1 of 1 test failed ==================
- Reviewing the logs it was apparent one of the RSA tests was failing.
- Upon further debugging it turned out the failure was a test in strongSwan that was attempting to create an RSA key size of 1536-bits.
Running case 'generate': DEBUG: key_sizes[_i] set to 1024 + PASS DEBUG: key_sizes[_i] set to 1536 - FAIL DEBUG: key_sizes[_i] set to 2048 + PASS DEBUG: key_sizes[_i] set to 3072 + PASS DEBUG: key_sizes[_i] set to 4096 + PASS
wolfSSL has a function RsaSizeCheck() which in FIPS mode will specifically reject any non FIPS RSA key sizes so this failure was not only expected, but it is a good thing for those wanting to use strongSwan in FIPS mode and ensure only FIPS-validated RSA key sizes will be supported!
wolfSSL is pleased that with the latest release of wolfSSL v4.7.0 and the wolfCrypt FIPS 140-2 module validated on FIPS certificate 3389, strongSwan support is working splendidly and wolfSSL engineers will be making efforts to ensure continued support into the future!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfMQTT Client Supports Microsoft Azure Sphere
Microsoft’s IoT Developer Advocate, Dave Glover, has put together an Azure Sphere Cloud example that uses the wolfMQTT client library and wolfSSL’s Embedded TLS library to demonstrate a secure IoT device connection using the Altair 8800 emulation project.
Find the project here and read more about Dave’s effort to get the Altair emulation connected to the Internet of Things!
Everyone deserves to have their IoT data secure, and wolfSSL provides the best libraries to accomplish that. Secure-IoT-Love from the wolfSSL team!
You can download the latest release here: https://www.wolfssl.com/download/
Or clone directly from our GitHub repository: https://github.com/wolfSSL/wolfMQTT
Don’t forget to add a star while you’re there!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Weekly updates
Archives
- July 2025 (5)
- June 2025 (22)
- May 2025 (25)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

