RECENT BLOG NEWS
wolfSentry Operating Environments
Our first preview release of wolfSentry, the IDPS (Intrusion Detection and Prevention System) for embedded and IoT systems, has platform support for Raspberry Pi, STM32 with CubeMX, Atmel ASF and Barebox. As well as native support for Microsoft Windows and Linux.
Here at wolfSSL we are always striving to be better so we would love to hear which operating environments and platforms you would like to see supported by wolfSentry.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfCrypt FIPS Operating Environments
wolfSSL fans! Do you like FIPS? Do you like virtual machines? Guess what. wolfSSL`s crypto library, wolfCrypt, is validated for FIPS 140-2 and in the process of being one of the first cryptography libraries to be validated for FIPS 140-3.
As wolfCrypt is commonly used in standard operating environments because of its royalty-free pricing and excellent cross platform support, wolfCrypt FIPS has been validated on a number of Operating Environments (OEs). The current validated OE list for both wolfCrypt FIPS certificates (#2425 and #3389) are listed here for reference.
Certificate #2425 Current OE List:
| Operating System | Processor | Platform |
|---|---|---|
| Linux 3.13 (Ubuntu) | Intel® Core™ i7-3720QM CPU @2.60GHz x 8 | HP EliteBook |
| iOS 8.1 | Apple™ A8 | iPhone™ 6 |
| Android 4.4 | Qualcomm Krait 400 | Samsung Galaxy S5 |
| FreeRTOS 7.6 | ST Micro STM32F | uTrust TS Reader |
| Windows 7 (64-bit) | Intel® Core™ i5 | Sony Vaio Pro |
| Linux 3.0 (SLES 11 SP4, 64-bit) | Intel® Xeon® E3-1225 | Imprivata OneSign |
| Linux 3.0 (SLES 11 SP4, 64-bit) on Microsoft Hyper-V 2012R2 Core | Intel® Xeon® E5-2640 | Dell® PowerEdge™ r630 |
| Linux 3.0 (SLES 11 SP4, 64-bit) on VMWare ESXi 5.5.0 | Intel® Xeon® E5-2640 | Dell® PowerEdge™ r630 |
| Windows 7 (64-bit) on VMWare ESXi 5.5.0 | Intel® Xeon® E5-2640 | Dell® PowerEdge™ r630 |
| Android Dalvik 4.2.2 | NXP i.MX6 | MXT‐700‐NC 7” touch panel |
| Linux 4.1.15 | NXP i.MX5 | NX‐1200 NetLinx NX Integrated Controller |
| Debian 8.8 | Intel Xeon® 1275v3 | CA PAM 304L Server |
| Windows Server 2012R2 | Intel® Xeon® E5335 | CA Technologies PAMHAF995 |
| Windows 7 Professional SP1 | Intel® Core™ i7‐2640M | Dell™ Latitude™ E6520 |
| Debian 8.7.0 | Intel ® Xeon® E3 Family with SGX support | Intel® x64 Server System R1304SP |
| Windows 10 Pro | Intel ® Core ™ i5 with SGX support | Dell™ Latitude™ 7480 |
| NET+OS v7.6 | Digi International NS9210 | Sigma IV infusion pump |
| Linux 4.4 (SLES 12 SP3, 64‐ bit) on Microsoft Hyper‐V 2016 Core | Intel® Xeon® E5‐2650 | Dell® PowerEdge™ r720 |
| Linux 4.4 (SLES 12 SP3, 64‐ bit) on VMWare ESXi 6.5.0 | Intel® Xeon® E5‐2403 | Dell® PowerEdge™ r420 |
Certificate #3389 Current OE List:
| Operating System | Processor | Platform |
|---|---|---|
| OpenRTOS v10.1.1 | STM32L4Rx | STMicroelectronics STM32L4R9I-DISCO (Discovery Kit) |
| HP Imaging & Printing Linux 4.9 | ARMv8 Cortex-A72/A53 | HP PN 3PZ95-60002 |
| Windows 10 Enterprise | Intel® Core™ i7-7820 x4 | Radar FCL Package Utility |
| Linux socfpga cyclone V | Armv7 rev 0, Cortex A-9 | SEL 2700 Series 24-Port Ethernet Switch |
| Fusion Embedded RTOS 5.0 | Analog Devices ADSP-BF516 (Blackfin) | Classone ® IP Radio Gateway |
| Linux 4.12 Yocto Standard | Freescale i.MX6 DualLite ARMv7 Cortex-A9 x2 | Metasys® SNC Series Network Control Engine |
| Nucleus 3.0 version 2013.08.1 | Freescale Vybrid VF500 | XL200 Radio |
| CodeOS v1.4 | CT8200 (ARM FA626TE) | HP ProLiant DL360 |
| Linux 4.14 | Armv8 Cortex-A53 | SEL-2742S |
| CMSIS-RTOS v2.1.3 | Silicon Labs EFM32G | Alto™ |
| Windows CE 6.0 | ARM Cortex-A8 | HP LaserJet Enterprise |
| QNX 6.6 | NXP i.MX 6SoloX Arm® Cortex®-A9 | Zebra ZT610 |
| QNX 7.0 | NXP i.MX7 Arm® Cortex®-A7 (x2) | Zebra ZD621 |
| QNX 6.5 | NXP i.MX25 Arm9™ | Zebra ZQ630 |
| QNX 7.0 | NXP i.MX 6ULL Arm® Cortex®-A7 | Zebra ZT421 |
| SUSE Linux Enterprise hosted in Hypervisor Vmware ESXi 6.7.0 | Intel® Xeon® E-2234 | Dell PowerEdge T340 |
| Linux 4.14 | Dual ARM Cortex A9 | Lenovo XClarity Controller |
| Swoop Kernel 1.5 | Xilinx Zynq Ultrascale+ XCZU9EG™ | Skipper |
| Windows Server 2016 | Intel® Xeon® E5-2603 | Dell PowerEdge R430 |
| NET+OS v7.6 | NS9210 | Sigma IV Infusion Pump |
| Windows 10 Pro | Intel® Core™ i7-7600U | Lenovo Thinkpad T470 |
| Windows Server 2019 | Intel® Xeon® Silver 4116 (x24) | HPE ProLiant DL360 |
| Android 11 | Qualcomm Snapdragon 865 (SoC) | Samsung Galaxy S20 5G |
| Linux 5.4 | Freescale i.MX7 Dual ARM® Cortex-A7 | iSTAR physical access controller |
| Linux 5.4 | Intel® Xeon® E-2244G | Dell PowerEdge R340 Rack Server |
| Linux 4.12 | Intel® Core™ i3-7101 | HP PageWide XL |
| Linux 4.9 | Freescale i.MX7 Dual ARM® Cortex-A7 | ZOLL Communications Module |
| NetBSD v6.0.1 | Intel(R) Atom(R) E3930 | RICOH IM C2500 |
| NetBSD v6.0.1 | Intel(R) Atom(R) E3940 | RICOH IM C6000 |
| Android 6.0 (Linux 4.1) | Freescale i.MX6 Quad/DualLite | RICOH IM C6000 |
| iOS 14 | Apple A14 Bionic | iPhone 12 |
| Android 8.1 (Linux 4.4) | Qualcomm Snapdragon 835 (APQ8098 / MSM8998) | EchoNous Kosmos® Bridge |
| CentOS Linux 7.9 on VMware ESXi 6.7 | Intel® Xeon® X5650 @2.67GHz | HP ProLiant DL360 |
| Linux 3.10 (CentOS 7) | Intel® Atom™ CPU D525 @1.80GHz | Beckman Coulter PROService RAP BOX |
| Yocto (dunfell) 3.1 | AMD GX-412TC SoC | LinkGuard |
| Linux 5.4 | Intel® Xeon® Gold 5218 CPU @ 2.30GHz | LiveAction LiveNX Appliance |
| Windows 10 Pro | Intel® Core™ i7-1255U @1.70 GHz | Dell Precision 3570 |
| FreeBSD 10.3 on VMWare ESXi 7.0 | Intel® Xeon® Silver 4210 @2.20GHz | Supermicro X11DPH-i (vnc-wolf) |
| Linux 5.15 on VMWare ESXi 7.0 | Intel® Xeon® Silver 4210 @2.20GHz | Supermicro X11DPH-i (sdlc-wolf) |
| Debian GNU/Linux 8 (jessie) | Broadcom BCM5634 | Corning 1LAN-SDDP-24POE (onl-armel) |
| Linux IPHO00550F22 4.1 | Broadcom BCM6858 | Corning 1LAN-SDAN-7691 (bcm6858x) |
| Debian GNU/Linux 8 (jessie) | Intel® Atom™ C2558 @ 2.40GHz | ufiSpace Cloud and Data Center Switch S7810-54QS (onl-x86_64) |
| Linux IPHO00559B23 3.4 | Broadcom BCM6838 | Corning 1LAN-SDAN-7290 (bcm683xx) |
| VxWorks 7 SR0630 | Intel® Core™ i7-5850EQ @2.70GHz | F-16 WASP |
| macOS Monterey 12.5 | Intel® Core™ i7-8569U @2.80GHz | MacBook Pro |
| macOS Monterey 12.5 | Apple M1 Max | MacBook Pro |
| Windows 11 Enterprise | Intel® Core™ i7-10610U @1.80GHz | Dell Latitude 7410 |
| Endace Crypto Firmware 1.0 | Intel® Xeon® Silver 4316 CPU @2.30GHz | EndaceProbe 2144 |
| macOS Monterey 12.5 | Apple M1 | MacBook Air |
| Vortec Scheduler | StarCore SC3850 DSP | Avaya MP160 |
| VxWorks 7 | NXP T1024 | G450 Media Gateway |
| VxWorks 6.9 | NXP MPC8650 | G430 Media Gateway |
| VxWorks 6.9 | TNETV1050 | Sectéra vIPer™ Phone |
| VxWorks 5.5 | Marvell Poncat2 Sheeva™ | ML6416E |
| Janteq Zynq Linux 5.4 | Xilinx Zynq-7000 SoC | AviTr3 |
| Janteq Zynq Linux 4.19 | Xilinx Zynq Ultrascale+ | Bronte3 |
| Janteq S5L Linux 4.9 | Ambarella S5L SoC | Maximo |
| Endace Crypto Firmware 1.0 | Intel® Xeon® Gold 6338N CPU @2.20GHz | EndaceProbe 2184 |
| Endace Crypto Firmware 1.0 | Intel® Xeon® Gold 5418N CPU @1.80GHz | EndaceProbe 94C8 |
| Endace Crypto Firmware 1.0 | Intel® Xeon® Gold 6230N CPU @2.30GHz | EndaceProbe 92C8 |
| Janteq iMX8QM Linux version 5.4 | i.MX8 Quad Max SoC | Flip2 |
| Android 13 | QualComm SnapDragon 8 SoC | Samsung Galaxy S22 |
wolfSSL can easily add additional OEs to existing wolfCrypt FIPS certificates.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
strongSwan + wolfSSL + FIPS!
As some may be aware, wolfSSL added support for strongSwan in April of 2019. The upstream commit can be reviewed here: https://github.com/strongswan/strongswan/pull/133
Users can test the latest development master of wolfSSL with the latest version of strongSwan using the following setup:
wolfSSL Build and Installation Steps
$ git clone https://github.com/wolfSSL/wolfssl.git $ cd wolfssl $ ./autogen.sh $ ./configure --enable-opensslall --enable-keygen --enable-rsapss --enable-des3 --enable-dtls --enable-certgen --enable-certreq --enable-certext --enable-sessioncerts --enable-crl --enable-ocsp CFLAGS="-DWOLFSSL_DES_ECB -DWOLFSSL_LOG_PRINTF -DWOLFSSL_PUBLIC_MP -DHAVE_EX_DATA" $ make $ make check $ sudo make install
strongSwan Build and Installation Steps
# if the following packages are not already installed: $ sudo apt-get install flex bison byacc libsoup2.4-dev gperf $ git clone https://github.com/strongswan/strongswan.git $ cd strongswan $ ./autogen.sh # if packages are missing autogen.sh must be re-run $ ./configure --disable-defaults --enable-pki --enable-wolfssl --enable-pem $ make $ make check $ sudo make install
wolfSSL has had interest in enabling FIPS 140-2/140-3 support with strongSwan so our engineers verified everything is working with the wolfCrypt FIPS 140-2 validated Module!
The steps wolfSSL used for testing are as follows:
Testing was done using the wolfSSL commercial FIPS release v4.7.0 which internally uses the wolfCrypt v4.0.0 FIPS 140-2 validated Crypto Module. It was located in the /home/user-name/Downloads directory on the target test system, Linux 4.15 Ubuntu 18.04 LTS running on Intel(R) Xeon(R) CPU E3-1270 v6 @ 3.80GHz.
- wolfSSL was configured and installed with these settings:
./configure --enable-opensslall --enable-keygen --enable-rsapss --enable-des3 --enable-dtls --enable-certgen --enable-certreq --enable-certext --enable-sessioncerts --enable-crl --enable-ocsp CFLAGS="-DWOLFSSL_DES_ECB -DWOLFSSL_LOG_PRINTF -DWOLFSSL_PUBLIC_MP -DHAVE_EX_DATA -DFP_MAX_BITS=8192" --enable-ed25519 --enable-curve25519 --enable-fips=v2 --enable-intelasm --prefix=$(pwd)/../fips-install-dir make make install
- A custom install location was used which equated to
/home/user-name/Downloads/fips-install-dirand the configuration for strongSwan accounted for this. - strongSwan was cloned to
/home/user-name/Downloadswith “git clone https://github.com/strongswan/strongswan.git” - StongSwan was configured and installed with these settings:
./configure --disable-defaults --enable-pki --enable-wolfssl --enable-pem --prefix=$(pwd)/../strongswan-install-dir wolfssl_CFLAGS="-I$(pwd)/../fips-install-dir/include" wolfssl_LIBS="-L$(pwd)/../fips-install-dir/lib -lwolfssl" make make install make check
- In the make check stage of the test, it was observed that 1 test was failing.
Passed 34 of 35 'libstrongswan' suites FAIL: libstrongswan_tests ================== 1 of 1 test failed ==================
- Reviewing the logs it was apparent one of the RSA tests was failing.
- Upon further debugging it turned out the failure was a test in strongSwan that was attempting to create an RSA key size of 1536-bits.
Running case 'generate': DEBUG: key_sizes[_i] set to 1024 + PASS DEBUG: key_sizes[_i] set to 1536 - FAIL DEBUG: key_sizes[_i] set to 2048 + PASS DEBUG: key_sizes[_i] set to 3072 + PASS DEBUG: key_sizes[_i] set to 4096 + PASS
wolfSSL has a function RsaSizeCheck() which in FIPS mode will specifically reject any non FIPS RSA key sizes so this failure was not only expected, but it is a good thing for those wanting to use strongSwan in FIPS mode and ensure only FIPS-validated RSA key sizes will be supported!
wolfSSL is pleased that with the latest release of wolfSSL v4.7.0 and the wolfCrypt FIPS 140-2 module validated on FIPS certificate 3389, strongSwan support is working splendidly and wolfSSL engineers will be making efforts to ensure continued support into the future!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
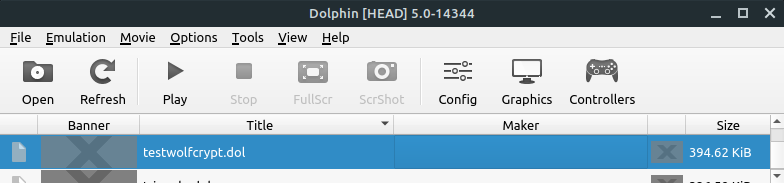
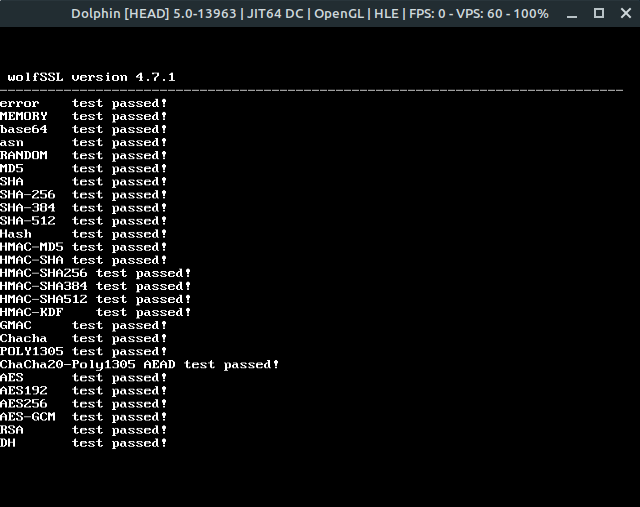
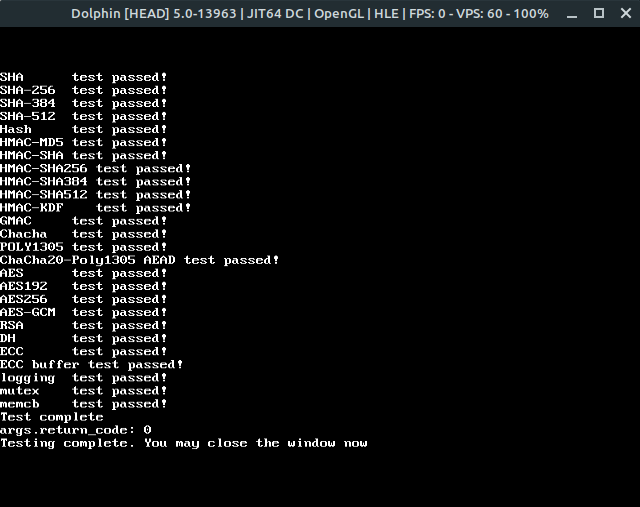
wolfSSL devkitPro Support
devkitPro is a set of tool chains for compiling to gaming platforms. This includes the Nintendo Switch, 3DS, Wii, and Gamecube. If you need cryptographic or SSL/TLS capabilities in your games then wolfSSL has support for compiling with devkitPro. wolfSSL is a very lightweight and fast SSL/TLS library that will fit perfectly in a constrained game console environment.
This blog will showcase how to compile the wolfSSL testwolfcrypt program for Wii and run it in the Dolphin Emulator. It assumes that the devkitPro was installed in /opt/.
Compile wolfSSL using the devkitPPC tool chain:
./autogen.sh
./configure CFLAGS='-DDOLPHIN_EMULATOR -DDEVKITPRO -DGEKKO -DNO_WRITEV -I/opt/devkitpro/libogc/include -mrvl -mcpu=750 -mno-eabi -MMD -MP' LDFLAGS='-L/opt/devkitpro/libogc/lib/wii -lwiiuse -lbte -logc -lm' CC=/opt/devkitpro/devkitPPC/bin/powerpc-eabi-gcc RANLIB=/opt/devkitpro/devkitPPC/bin/powerpc-eabi-ranlib --host=ppc --enable-cryptonly --disable-shared --enable-static --disable-filesystem
make
Then convert the binary to a .dol file:
/opt/devkitpro/tools/bin/elf2dol wolfcrypt/test/testwolfcrypt ../testwolfcrypt.dol
The above command places the resulting binary in the directory that contains the wolfssl directory. Navigate to this directory in the Dolphin Emulator and run it:
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
wolfSSL Asynchronous Release v4.7.0
The wolfSSL / wolfCrypt libraries support asynchronous (non-blocking) crypto using hardware acceleration with the Intel QuickAssist and Cavium Nitrox III/V adapters. These are PCIe devices that accelerate crypto operations. For server platforms requiring high connection rates and throughput this allows greatly increased performance.
For some performance numbers see this page: https://www.wolfssl.com/docs/intel-quickassist/
Release v4.7.0 of wolfSSL Async has bug fixes and new features including:
- All wolfSSL v4.7.0 release fixes (https://github.com/wolfSSL/wolfssl/releases/tag/v4.7.0-stable)
- Fix for ARC4 macro typo.
- Fixes for Cavium Nitrox and Intel Quick Assist (https://github.com/wolfSSL/wolfssl/pull/3577) with TLS v1.3
- Documentation updates.
- Fixes for asynchronous memory leaks (https://github.com/wolfSSL/wolfssl/pull/3227)
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
BSD Kernel Mode compatibility for wolfSSL
We are in the process of adding BSD Kernel compatibility to wolfSSL. This means that our embedded SSL library would run in Kernel mode and use BSD based OE’s. The advantage of this project may include performance enhancement for device driver implementers that want SSL security. Stay tuned for more updates regarding this project. We would love to know do Kernel developers want an SSL library? Please comment!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
cURL Release – cURL 7.77.0 – 200 OK
This post has been cross posted from Daniel Stenberg’s blog – originally posted here.
Welcome to the 200th curl release. We call it 200 OK. It coincides with us counting more than 900 commit authors and surpassing 2,400 credited contributors in the project. This is also the first release ever in which we thank more than 80 persons in the RELEASE-NOTES for having helped out making it and we’ve set two new record in the bug-bounty program: the largest single payout ever for a single bug (2,000 USD) and the largest total payout during a single release cycle: 3,800 USD.
This release cycle was 42 days only, two weeks shorter than normal due to the previous 7.76.1 patch release.
Numbers
- the 200th release
- 5 changes
- 42 days (total: 8,468)
- 133 bug-fixes (total: 6,966)
- 192 commits (total: 27,202)
- 0 new public libcurl function (total: 85)
- 2 new curl_easy_setopt() option (total: 290)
- 2 new curl command line option (total: 242)
- 82 contributors, 44 new (total: 2,410)
- 47 authors, 23 new (total: 901)
- 3 security fixes (total: 103)
- 3,800 USD paid in Bug Bounties (total: 9,000 USD)
Security
We set two new records in the curl bug-bounty program this time as mentioned above. These are the issues that made them happen.
This is a Use-After-Free in the OpenSSL backend code that in the absolutely worst case can lead to an RCE, a Remote Code Execution. The flaw is reasonably recently added and it’s very hard to exploit but you should upgrade or patch immediately.
The issue occurs when TLS session related info is sent from the TLS server when the transfer that previously used it is already done and gone.
The reporter was awarded 2,000 USD for this finding.
When libcurl accepts custom TELNET options to send to the server, it the input parser was flawed which could be exploited to have libcurl instead send contents from the stack.
The reporter was awarded 1,000 USD for this finding.
In the Schannel backend code, the selected cipher for a transfer done with was stored in a static variable. This caused one transfer’s choice to weaken the choice for a single set transfer could unknowingly affect other connections to a lower security grade than intended.
The reporter was awarded 800 USD for this finding.
Changes
In this release we introduce 5 new changes that might be interesting to take a look at!
- Make TLS flavor explicit
As explained separately, the curl configure script no longer defaults to selecting a particular TLS library. When you build curl with configure now, you need to select which library to use. No special treatment for any of them!
- No more SSL
curl now has no more traces of support for SSLv2 or SSLv3. Those ancient and insecure SSL versions were already disabled by default by TLS libraries everywhere, but now it’s also impossible to activate them even in special build. Stripped out from both the curl tool and the library (thus counted as two changes).
- HSTS in the build
We brought HSTS support a while ago, but now we finally remove the experimental label and ship it enabled in the build by default for everyone to use it more easily.
- In-memory cert API
We introduce API options for libcurl that allow users to specify certificates in-memory instead of using files in the file system. See CURLOPT_CAINFO_BLOB.
Favorite bug-fixes
Again we manage to perform a large amount of fixes in this release, so I’m highlighting a few of the ones I find most interesting!
- Version output
The first line of curl -V output got updated: libcurl now includes OpenLDAP and its version of that was used in the build, and then the curl tool can add libmetalink and its version of that was used in the build!
- curl_mprintf: add description
We’ve provided the *printf() clone functions in the API since forever, but we’ve tried to discourage users from using them. Still, now we have a first shot at a man page that clearly describes how they work.
This is important as they’re not quite POSIX compliant and users who against our advice decide to rely on them need to be able to know how they work!
- CURLOPT_IPRESOLVE: preventing wrong IP version from being used
This option was made a little stricter than before. Previously, it would be lax about existing connections and prefer reuse instead of resolving again, but starting now this option makes sure to only use a connection with the request IP version.
This allows applications to explicitly create two separate connections to the same host using different IP versions when desired, which previously libcurl wouldn’t easily let you do.
- Ignore SIGPIPE in curl_easy_send
libcurl makes its best at ignoring SIGPIPE everywhere and here we identified a spot where we had missed it… We also made sure to enable the ignoring logic when built to use wolfSSL.
- Several HTTP/2-fixes
There are no less than 6 separate fixes mentioned in the HTTP/2 module in this release. Some potential memory leaks but also some more behavior improving things. Possibly the most important one was the move of the transfer-related error code from the connection struct to the transfers struct since it was vulnerable to a race condition that could make it wrong. Another related fix is that libcurl no longer forcibly disconnects a connection over which a transfer gets HTTP_1_1_REQUIRED returned.
- Partial CONNECT requests
When the CONNECT HTTP request sent to a proxy wasn’t all sent in a single send() call, curl would fail. It is baffling that this bug hasn’t been found or reported earlier but was detected this time when the reporter issued a CONNECT request that was larger than 16 kilobytes…
- TLS: add USE_HTTP2 define
There was several remaining bad assumptions that HTTP/2 support in curl relies purely on nghttp2. This is no longer true as HTTP/2 support can also be provide by hyper.
- normalize numerical IPv4 hosts
The URL parser now knows about the special IPv4 numerical formats and parses and normalizes URLs with numerical IPv4 addresses.
- Timeout, timed out libssh2 disconnects too
When libcurl (built with libssh2 support) stopped an SFTP transfer because a timeout was triggered, the following SFTP disconnect procedure was subsequently also stopped because of the same timeout and therefore wasn’t allowed to properly clean up everything, leading to a memory-leak!
IRC network switch
We moved the #curl IRC channel to the new network libera.chat. Come join us there!
Next release
On Jul 21, 2021 we plan to ship the next release. The version number for that is not yet decided but we have changes in the pipeline, making a minor version number bump very likely.
Support
- wolfSSL offers Curl support is available, and part of that support revenue goes into finding and fixing these kinds of vulnerabilities.
- Customers under curl support can get advice on whether or not the advisories apply to them.
- 24×7 support on curl is available, and can include pre-notification of upcoming vulnerability announcements.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Command-line Utility: Here’s What We’re Adding Next
wolfSSL has a command-line utility, it’s called wolfCLU. As promised, here’s a sneak peek of notable additions to wolfCLU that are coming soon:
- PKEY and certificate public key output
- Certificate request creation
- Updates to human readable text output of certificates
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Download wolfCLU: https://github.com/wolfSSL/wolfssl-examples/tree/master/wolfCLU
Love it? Star us on GitHub!
Did You Know We Have a Command-line Utility?
In case you didn’t know, wolfSSL has a portable command line utility. You can download wolfCLU on Github today for use with the wolfSSL embedded SSL/TLS library! wolfCLU (Command Line Utility) is backed by the best-tested crypto using wolfCrypt and it can make use of FIPS builds with wolfSSL!
wolfCLU currently has the following features:
– Support for ED25519 sign and verify
– Autoconf for portability
– Encrypt a file and store it locally on your computer
– Decrypt that file after it has been encrypted, or send it via email to your friend, if he/she knows the password and algorithm used for encryption, they can then decrypt it on their computer
– Hash a single file (IE a zip archive) for verification
– Benchmark the currently configured Algorithms
– X509 parsing and print out
Download wolfCLU: https://github.com/wolfssl/wolfclu
Love it? Star us on GitHub!
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Advantages of using wolfTPM with ST33 TPM 2.0
wolfTPM is the only TPM 2.0 library designed for baremetal and embedded systems. It also has native Windows and Linux support, alongside a TPM simulator for rapid development and testing.
When it comes to choosing a TPM 2.0 dedicated chip for your project, there are multiple options: Nuvoton NPCT75x, STMicroelectronics ST33, Infineon SLB9670, Microchip ATTPM20P, etc.
Here are our highlights when using ST33 chip with wolfTPM:
- Only wolfTPM supports GPIO control for ST33
- Depending on the chip variant, a ST33 could offer up to four(4) extra GPIO
- The access to these GPIO is protected by the TPM 2.0 authorization
- Making the GPIO control offered by wolfTPM a great tool for signaling across subsystems for critical, important or security events
- wolfTPM also provides an open-source example code ready for use
- ST33 has the most Non-volatile memory storage on the market, right now
- Typically, TPM 2.0 NVRAM storage is limited, this makes ST33 stand out. Multiple certificates and keys can be stored in the ST33 non-volatile memory
- wolfTPM offers open-source examples on how to securely store secrets and keys in the TPM’s NVRAM
- Using ST33 for Automotive, Industrial, Medical and Aerospace devices with wolfTPM is easy
- Critical-safety systems often use state machines and RTOS
- Baremetal and RTOS do not provide driver for TPM 2.0
- Thanks to wolfTPM’s design, using ST33 without a driver is possible
- wolfTPM has its own internal TIS layer and direct support for I2C and SPI
- Using ST33 for IoT devices with wolfTPM is highly recommended, because our TPM 2.0 stack is lightweight. In comparison with other libraries, wolfTPM produces 20 times less code and 100 times less memory.
- Only ST33 supports AES symmetric operations for encryption and decryption by default, using TPM2_EncryptDecrypt2. Other TPM 2.0 modules support by default only AES CFB for parameter encryption.
If you have any questions or run into any issues, contact us at facts@wolfssl.com, or call us at +1 425 245 8247.
Weekly updates
Archives
- June 2025 (21)
- May 2025 (25)
- April 2025 (24)
- March 2025 (22)
- February 2025 (21)
- January 2025 (23)
- December 2024 (22)
- November 2024 (29)
- October 2024 (18)
- September 2024 (21)
- August 2024 (24)
- July 2024 (27)
- June 2024 (22)
- May 2024 (28)
- April 2024 (29)
- March 2024 (21)
- February 2024 (18)
- January 2024 (21)
- December 2023 (20)
- November 2023 (20)
- October 2023 (23)
- September 2023 (17)
- August 2023 (25)
- July 2023 (39)
- June 2023 (13)
- May 2023 (11)
- April 2023 (6)
- March 2023 (23)
- February 2023 (7)
- January 2023 (7)
- December 2022 (15)
- November 2022 (11)
- October 2022 (8)
- September 2022 (7)
- August 2022 (12)
- July 2022 (7)
- June 2022 (14)
- May 2022 (10)
- April 2022 (11)
- March 2022 (12)
- February 2022 (22)
- January 2022 (12)
- December 2021 (13)
- November 2021 (27)
- October 2021 (11)
- September 2021 (14)
- August 2021 (10)
- July 2021 (16)
- June 2021 (13)
- May 2021 (9)
- April 2021 (13)
- March 2021 (24)
- February 2021 (22)
- January 2021 (18)
- December 2020 (19)
- November 2020 (11)
- October 2020 (3)
- September 2020 (20)
- August 2020 (11)
- July 2020 (7)
- June 2020 (14)
- May 2020 (13)
- April 2020 (14)
- March 2020 (4)
- February 2020 (21)
- January 2020 (18)
- December 2019 (7)
- November 2019 (16)
- October 2019 (14)
- September 2019 (18)
- August 2019 (16)
- July 2019 (8)
- June 2019 (9)
- May 2019 (28)
- April 2019 (27)
- March 2019 (15)
- February 2019 (10)
- January 2019 (16)
- December 2018 (24)
- November 2018 (9)
- October 2018 (15)
- September 2018 (15)
- August 2018 (5)
- July 2018 (15)
- June 2018 (29)
- May 2018 (12)
- April 2018 (6)
- March 2018 (18)
- February 2018 (6)
- January 2018 (11)
- December 2017 (5)
- November 2017 (12)
- October 2017 (5)
- September 2017 (7)
- August 2017 (6)
- July 2017 (11)
- June 2017 (7)
- May 2017 (9)
- April 2017 (5)
- March 2017 (6)
- January 2017 (8)
- December 2016 (2)
- November 2016 (1)
- October 2016 (15)
- September 2016 (6)
- August 2016 (5)
- July 2016 (4)
- June 2016 (9)
- May 2016 (4)
- April 2016 (4)
- March 2016 (4)
- February 2016 (9)
- January 2016 (6)
- December 2015 (4)
- November 2015 (6)
- October 2015 (5)
- September 2015 (5)
- August 2015 (8)
- July 2015 (7)
- June 2015 (9)
- May 2015 (1)
- April 2015 (4)
- March 2015 (12)
- January 2015 (4)
- December 2014 (6)
- November 2014 (3)
- October 2014 (1)
- September 2014 (11)
- August 2014 (5)
- July 2014 (9)
- June 2014 (10)
- May 2014 (5)
- April 2014 (9)
- February 2014 (3)
- January 2014 (5)
- December 2013 (7)
- November 2013 (4)
- October 2013 (7)
- September 2013 (3)
- August 2013 (9)
- July 2013 (7)
- June 2013 (4)
- May 2013 (7)
- April 2013 (4)
- March 2013 (2)
- February 2013 (3)
- January 2013 (8)
- December 2012 (12)
- November 2012 (5)
- October 2012 (7)
- September 2012 (3)
- August 2012 (6)
- July 2012 (4)
- June 2012 (3)
- May 2012 (4)
- April 2012 (6)
- March 2012 (2)
- February 2012 (5)
- January 2012 (7)
- December 2011 (5)
- November 2011 (7)
- October 2011 (5)
- September 2011 (6)
- August 2011 (5)
- July 2011 (2)
- June 2011 (7)
- May 2011 (11)
- April 2011 (4)
- March 2011 (12)
- February 2011 (7)
- January 2011 (11)
- December 2010 (17)
- November 2010 (12)
- October 2010 (11)
- September 2010 (9)
- August 2010 (20)
- July 2010 (12)
- June 2010 (7)
- May 2010 (1)
- January 2010 (2)
- November 2009 (2)
- October 2009 (1)
- September 2009 (1)
- May 2009 (1)
- February 2009 (1)
- January 2009 (1)
- December 2008 (1)

